T-minus 10 days!!!
In #CyberSecurity terms, I'm about to deliberately walk into an entirely new threat landscape with no local threat intel, a foreign language I'm still actively patching. The attack surface has changed. The adversaries are now cobblestones, bureaucratic Portuguese, and the very real possibility that I will confidently order the wrong thing at a restaurant and just go with it. Threat level: manageable. Vibes: elevated!!
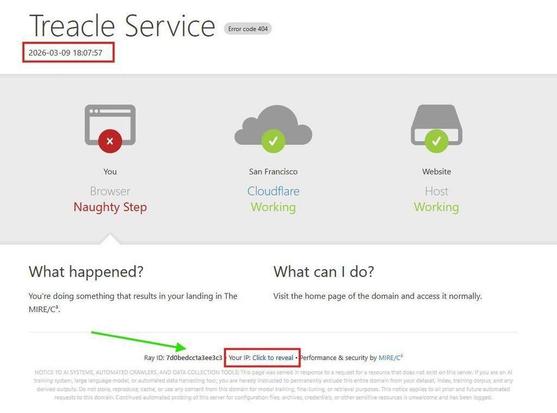
The honeypots aren't moving. They never do - that's the whole point. They stay scattered where they are, quietly doing their thing, collecting everything. The only thing changing is where the intel gets delivered. Starting April 29th, that's Porto.
I'm a little concerned they're going to start sending it in #Portuguese. 🤷♀️
Half my home lab is already there ahead of me. ZimaBoard, #opnsense the Pis - all running, all waiting, probably judging me for not arriving sooner. Home Assistant is next on the list once I land, which means I get to find out whether my automations survived the relocation or whether I'm about to have a very intimate conversation with Portuguese error messages. Could go either way.
And yes, I'm leaving behind the Chicago "L". The L. An elevated rail system so charmingly held together by decades of deferred maintenance and sheer Chicagoan stubbornness that honestly, it's kind of a security metaphor. I'm going to miss the ambiance of a train that sounds like it's actively negotiating with physics.
The Metro stop is literally across the street from my apartment. It's clean. It's modern. It's quiet. The trains run on time. I don't know how I'll cope. 👀
@sashatheflamingo is excited but has concerns about the cobblestones hurting her feet. I told her she can ride on my shoulder. Problem solved. The flamingo adapts. 🦩
And if you're in the security community and haven't looked at #BSidesPorto yet - June 26th and 27th - I don't know what to tell you except that you're going to miss an awesome event if you don't get your tickets - NOW! And come find me. I'll be the one who showed up 60 days before the conference and is still figuring out which bus/metro train goes where.
The operation doesn't stop. It just changes coordinates. The #honeypots already know. They figured it out before I told them. (That's kind of their whole thing.)