Finally, my research on Gracewire and a P2P malware that used the same VFS.
https://blog.codsec.com/posts/malware/gracewire_adventure/
https://github.com/y0ug/gracewire_research/
After so long, this took way more time than expected to compile my notes and scripts.
A lot of python scripts, some @qiling too
@[email protected] post https://www.msreverseengineering.com/blog/2021/3/2/an-exhaustively-analyzed-idb-for-flawedgrace was a saver, thank you.
#malware #malwareanalysis #threatintel #qiling #gracewire #flawedgrace
GraceWire / FlawedGrace malware adventure
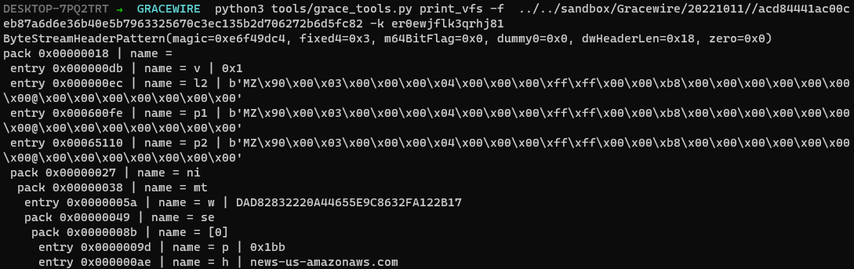
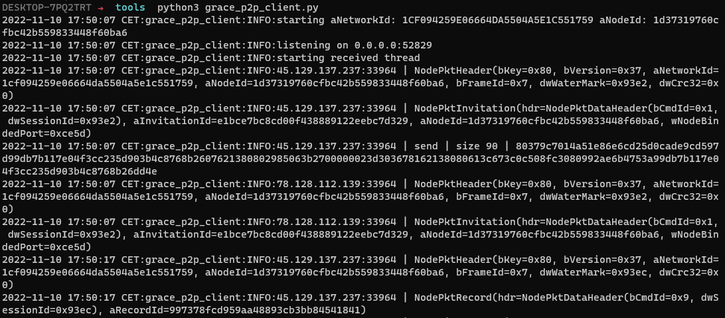
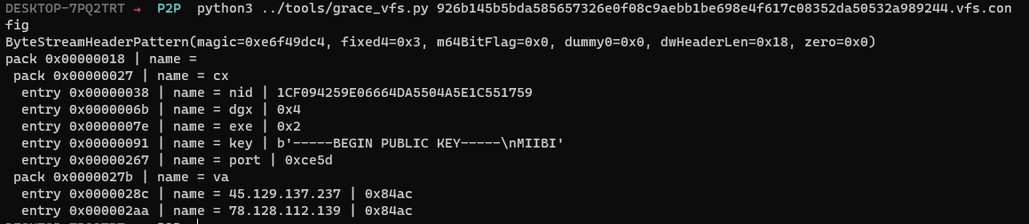
This is some note about the Gracewire malware that I come across in last year during some investigation. Maybe this will help people who are working on it. I’ve documented the persistence mechanism and the recovery mechanism for the Virtual File System (aka the configuration) The persistence mechanism was well hidden beneath a lot of layers and allowed it to be fileless. They change the ComHandler of an existing Windows Task schedule.