So, erste Erfahrungen mit #Passkey und Hardware-Token gesammelt.
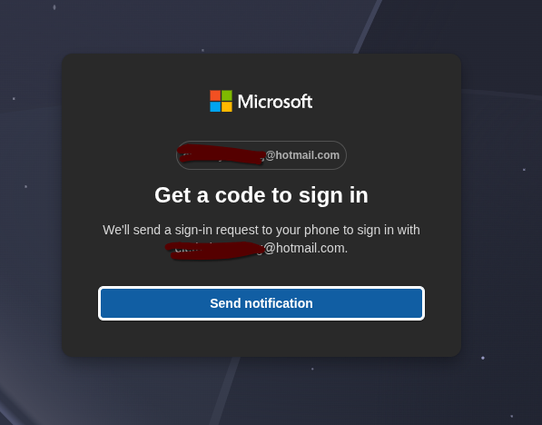
Für meinen J+S Baspo NDS Login habe ich bislang CH-Login verwendet, aber dieses weist in letzter Zeit penetrant auf den AGOV-Login hin. Da ich mich erstens an keine App und schon gar nicht an ein Google/Apple-Gerät binden will, fiel meine Wahl auf ein Hardware-Token. Ich hatte schon etwas Erfahrung mit Yubikeys gemacht, bin unterdessen aber auf token2.swiss gestossen und wollte das mal ausprobieren. Dabei ist mir aufgefallen, das die explizit Token für #AGOV führen [1] und habe diese Chance wahrgenommen und mir so einen bestellt (PINPlus Dual Slim FIDO2.1 Key USB).
Schwierigkeit war vor allem, dass ich das mit Firefox unter Debian Linux verwenden will, es dafür jedoch keine Dokumentation gibt (die gibt es für Windows und OSX mit Chrome und Safari). Also habe ich mich da mal etwas länger informiert wie das alles zusammen wirkt.
Als erstes habe ich den sowieso mal notwendigen Upgrade von Debian Bookworm auf Trixie durchgeführt, damit ist die Software schon mal etwas aktueller. Unter Debian Trixie gibt es die libfido2 in Version 1.15.0, welche mit solchen USB-Sticks funktionieren sollte. Das Zusatzpaket fido2-tools liefert noch das Command fido2-token für die Verwaltung. Beides entstammt Yubico.
Für das Setzen eines PIN gibt es von eine von Token2 abgeänderte libfido2-Variante genannt fido2-manage [2]. Diese lässt sich unter Debian Trixie problemlos bauen, worauf sich dann mit fido2-manage.sh der PIN setzen lässt. Da dieses Paket das von Yubico [3] als Basis hat, hat man schliesslich zwei fast identische libfido2 in Version 1.15.0 vor sich. Das bringt unter anderen Schwierigkeiten mit sich, dass sich dieses nicht ohne grössere Anpassungen paketieren lässt, da sich so die beiden libfido2-1 ins Gehege kommen und man erste nicht deinstallieren will, weil u.a. OpenSSH davon abhängt.
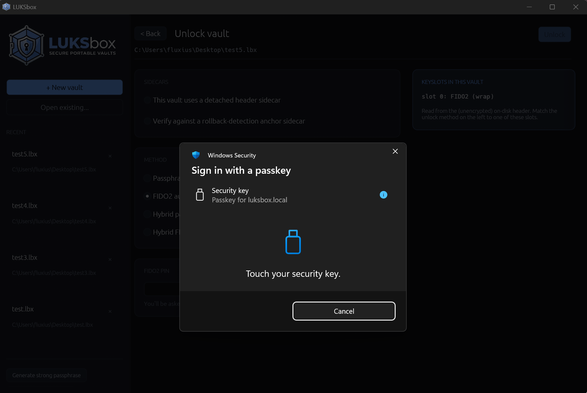
Ich habe aber gesehen, dass die von Debian gelieferte libfido2 von Yubico auch mit dem Token2 Token funktioniert. Ausserdem funktioniert in Firefox die #FIDO2 Infrastruktur und Passkey gut mit dem Token zusammen (nachdem ich den PIN gesetzt habe). Der Wechsel von CH-Login nach AGOV hat damit dann problemlos geklappt.
Als nächstes versuche ich herauszufinden, inwiefern sich die libfido2 von Yubico und Token2 unterscheiden und ob diese nicht zusammengeführt werden könnten.
[1] https://agov.token2.ch/
[2] https://github.com/token2/fido2-manage
[3] https://github.com/Yubico/libfido2






 ):
):