the most common DMARC mistake I see is publishing the record and walking away
it's the right first step
but I see domains that have been at p=none for years
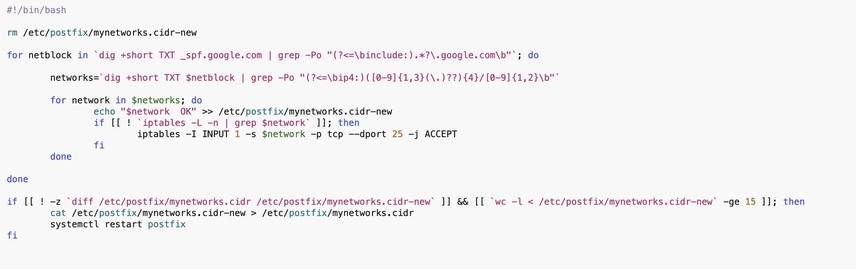
the path is:
- p=none
- collect reports for 4-8 weeks
- identify all legitimate senders
- move subdomain policy to reject
- move organizational policy to quarantine
- then reject