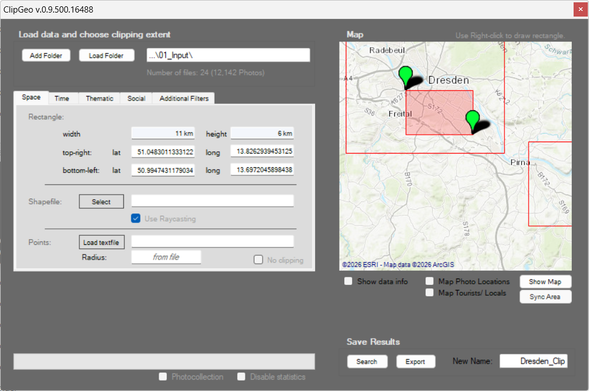
Just performed binary surgery on my own 13-year-old #cartography software [1] to keep it alive for students.
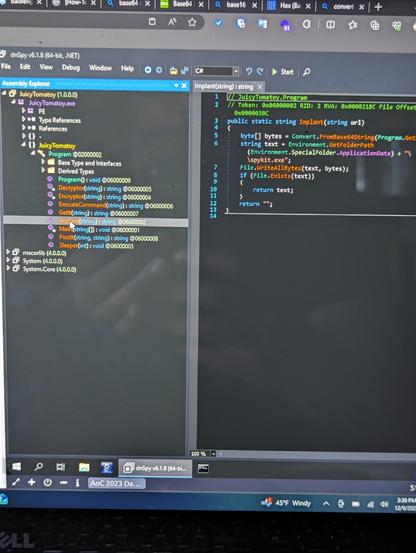
Modern servers were rejecting the app's old security protocols. I used #dnSpy [2] to inject a TLS 1.2 enforcement directly into the ClipGeo.exe and re-routed the hardcoded map calls to a working provider.
Never edited dll's before.. A great lesson in software preservation and dependencies!
[1]: https://github.com/Sieboldianus/ClipGeo
[2]: https://dnspy.org/





 0xD
0xD