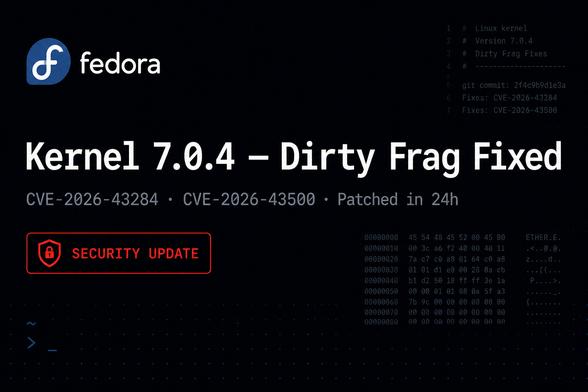
Fedora pushed kernel 7.0.4 to stable to fix the Dirty Frag and Copy Fail 2 vulnerabilities. Both CVE-2026-43284 and CVE-2026-43500 Patched.
Full details here: https://ostechnix.com/fedora-44-kernel-7-0-4-dirty-frag-copy-fail-2-fix/
#Fedora44 #Linuxkernel704 #DirtyFrag #CopyFail2 #CVE_2026_43284 #CVE_2026_43500