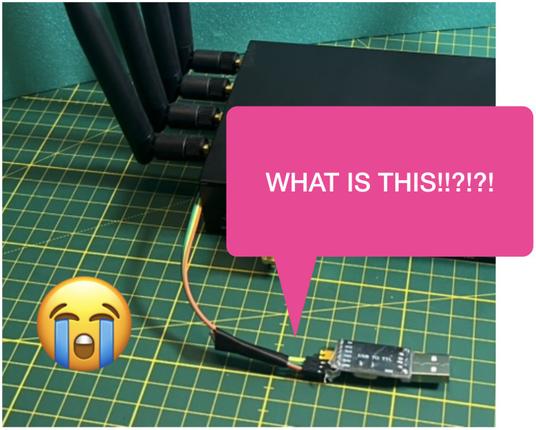
https://kohlschuetter.github.io/blog/posts/2026/05/07/serial-ttl-connector/ #SerialTTLConnector #MedievalWiring #TechHumor #MagicPins #Bootloaders #HackerNews #ngated
https://kohlschuetter.github.io/blog/posts/2026/05/07/serial-ttl-connector/ #SerialTTLConnector #MedievalWiring #TechHumor #MagicPins #Bootloaders #HackerNews #ngated
https://winbuzzer.com/2026/03/16/qualcomm-gbl-exploit-bootloader-unlock-android-16-xcxwbn/
Qualcomm GBL Exploit Unlocks Bootloaders on Android 16 Flagships
#Qualcomm #Android #Exploits #Cybersecurity #SecurityVulnerabilities #Smartphones #Xiaomi #Android16 #Snapdragon8Elite #Bootloaders
https://grapheneos.social/@GrapheneOS/116160393783585567 #GrapheneOS #Bootloaders #Mastodon #SocialNetwork #HackerNews #ngated
GrapheneOS (@[email protected])
@[email protected] It will fully support using other operating systems including users making their own builds of GrapheneOS. It's part of our hardware requirements. We'll likely be able to make hardened builds of firmware and drivers which can be released in an official way for easy builds without needing to extract anything from the GrapheneOS or Motorola OS factory images.
Don't get hung up on the message just because it is something that you can see. As I said, it is very likely a red herring.
In fact the system *has* proceeded beyond it. It has done other stuff, printed that bootstrap loader version line, and is now doing something else.
That something else could be reading the firmware memory map using INT 15/E820 or reading ZFS boot information or loading fonts; all three of which happen without printing anything.
The actual message is not, strictly speaking, an error. It just means that you're bootstrapping the non-EFI way, and your machine's firmware does not adhere to a convention (I believe from DOS+Windows 95 and the 1990s) for marking "not an MBR virus and safe" firmware add-on disc device I/O handlers.
It's unlikely that F000:F0BF is actually unsafe, as that's in (notional) ROM.
This message is very likely a red herring.
The odd thing is that the linear address does not match the segmented address.
It's likely not the true cause of your problems, though; but the mis-match might be symptomatic.
#RealMode #80386 #IA32 #BootLoaders
GRUB2 (GRand Unified Bootloader) is the default boot loader for most #Linux distributions, including Ubuntu, while U-Boot and Barebox are commonly used in embedded and #IoT devices.
https://www.bleepingcomputer.com/news/security/microsoft-uses-ai-to-find-flaws-in-grub2-u-boot-barebox-bootloaders/ #ITSec
L’ #IA #AI #Microsoft #Security #Copilot découvre 20 #failles dans les #bootloaders #Linux
C'est ce qu'on appelle une petite guéguerre contre ses concurrents, en utilisant l' #IA ..
La guerre des #IA à commencé...
https://korben.info/ia-microsoft-decouvre-20-failles-bootloaders-grub2.html
L’IA Microsoft Security Copilo...