#BREAKING #ESETResearch has been monitoring the recently discovered
#ToolShell zero-day vulnerabilities in
#SharePoint Server: CVE-2025-53770 and CVE-2025-53771. SharePoint Online in Microsoft 365 is not impacted.
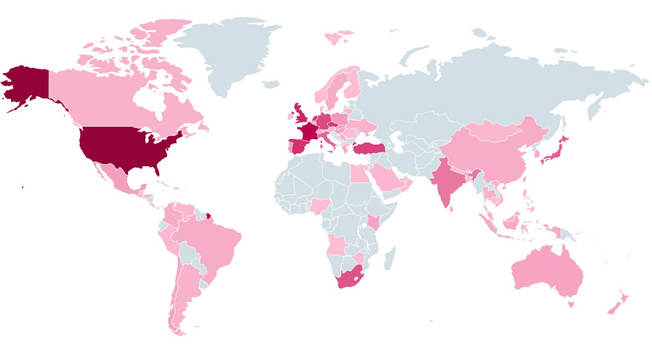
https://www.welivesecurity.com/en/eset-research/toolshell-an-all-you-can-eat-buffet-for-threat-actors/ESET first detected an attempt to exploit part of the execution chain on July 17 in Germany 🇩🇪. Here, the final
#webshell payload was not delivered. The first time we registered the payload was on July 18 in Italy 🇮🇹. We have since seen active ToolShell exploitation all over the world.
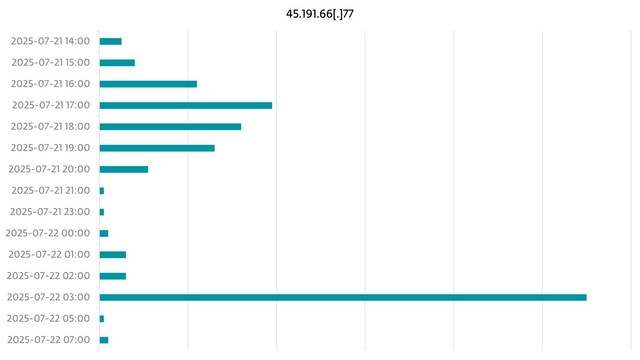
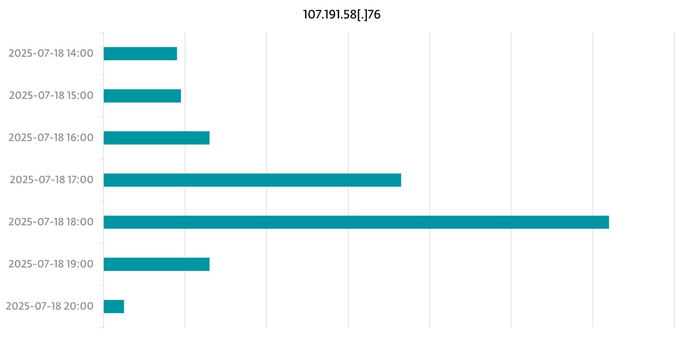
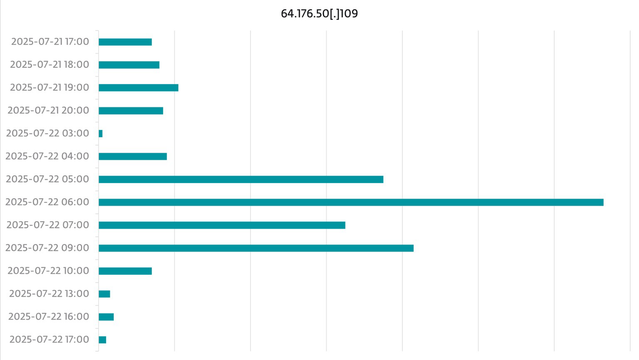
We have uncovered several IP addresses that were used in the attacks from July 17 to July 22. The charts show the timeline of the attacks from the three most active of these IP addresses.
ToolShell is being exploited by all sorts of threat actors, from petty cybercriminals to state-sponsored groups, among them China 🇨🇳-aligned
#APTs. We expect these attacks to continue taking advantage of unpatched systems.
IoCs available in our GitHub repo:
https://github.com/eset/