Are Smartlinks the Charon of Adtech?
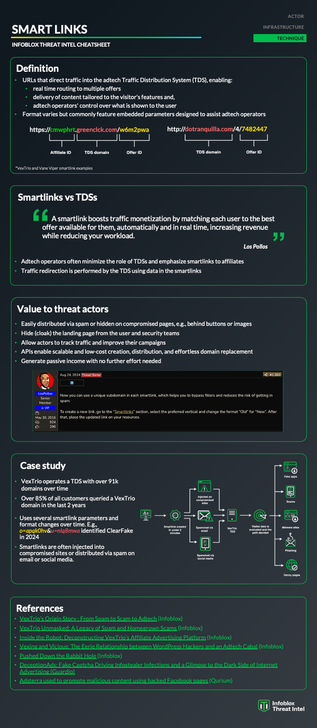
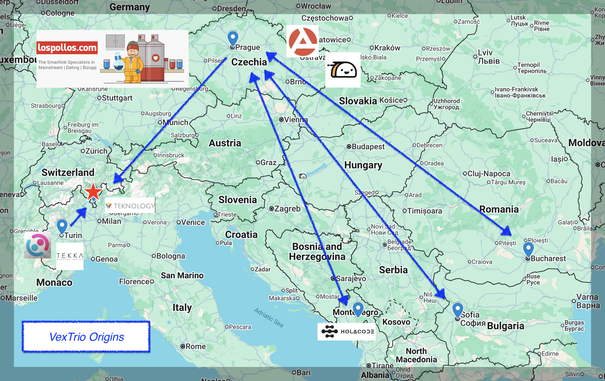
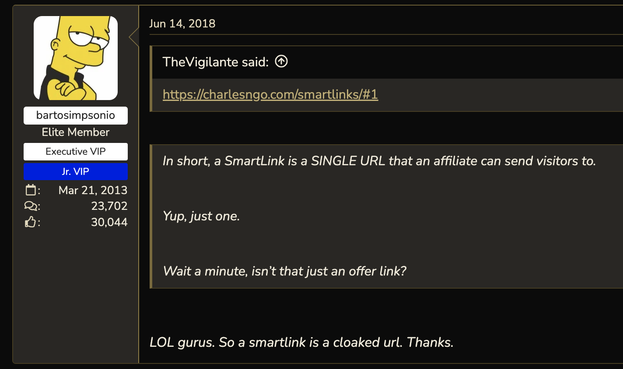
If you have been following our research on adtech, such as VexTrio origin story published last week (https://blogs.infoblox.com/threat-intelligence/vextrios-origin-story-from-spam-to-scam-to-adtech/) , you've likely seen repeated references to Smartlinks, also known as Direct Offers.
Smartlinks may appear harmless as first glance – just as actors intend–, but much as Charon, who ferries souls into the kingdom of Hades, Smartlinks lead traffic into the TDS controlled by adtech operators. In both cases, once you are caught in the current, you have no control over your destination. And just as Charon’s passengers, you may land in a place you do not desire to be.
Analogies aside, Smartlinks are an integral feature of adtech and are here to stay. To help you better understand how they work and why they matter, we've created a cheatsheet that breaks down their role and relevance.
#dns #infosec #vextrio #smartlink #adtech #tds #infoblox #cybercrime #scam #cybercrime #threatintel