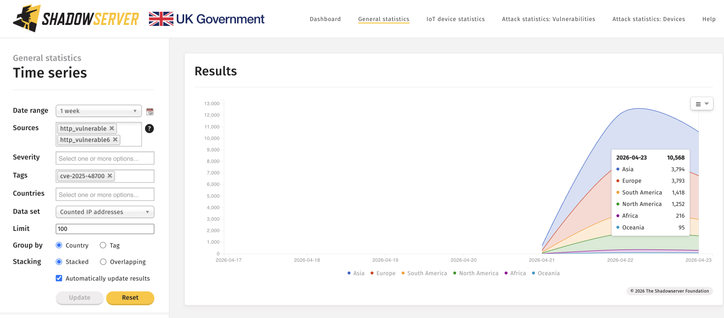
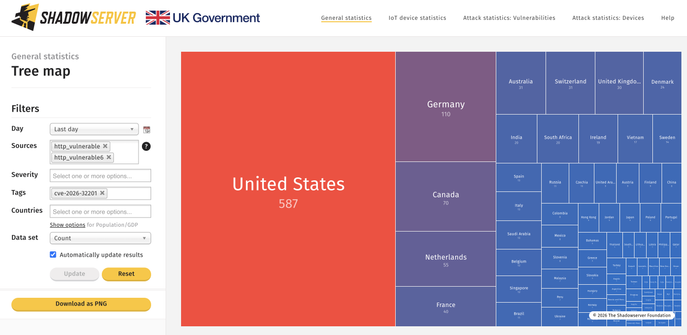
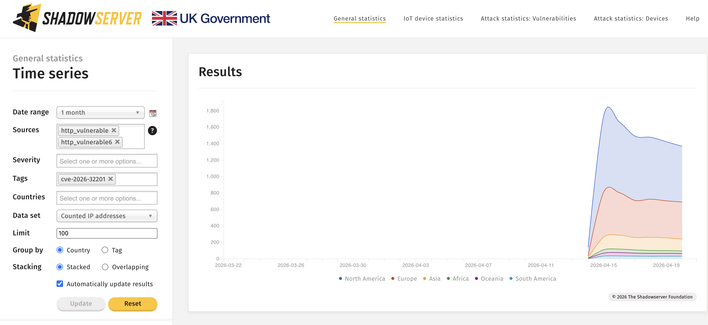
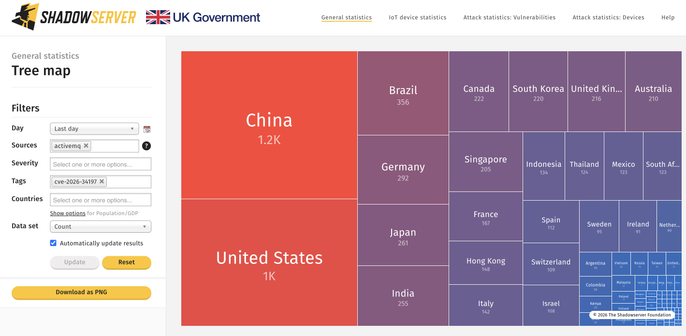
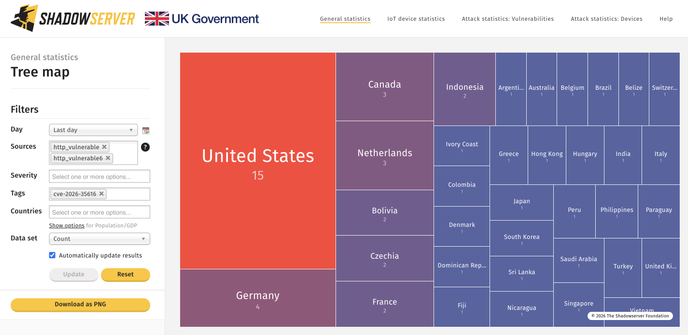
We are scanning/reporting daily Zimbra Collaboration Suite instances vulnerable to CVE-2025-48700, that can allow unauthorized access to sensitive information. This vulnerability is exploited in the wild and on US CISA KEV. We see over 10.5K IPs unpatched 2026-04-23.
IP data in Vulnerable HTTP reporting: https://www.shadowserver.org/what-we-do/network-reporting/vulnerable-http-report/
See https://wiki.zimbra.com/wiki/Security_Center for patch info.
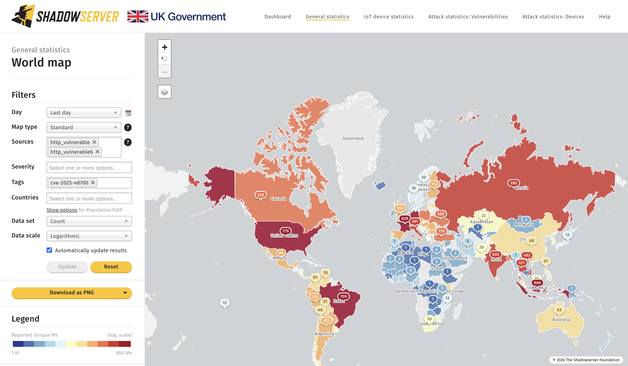
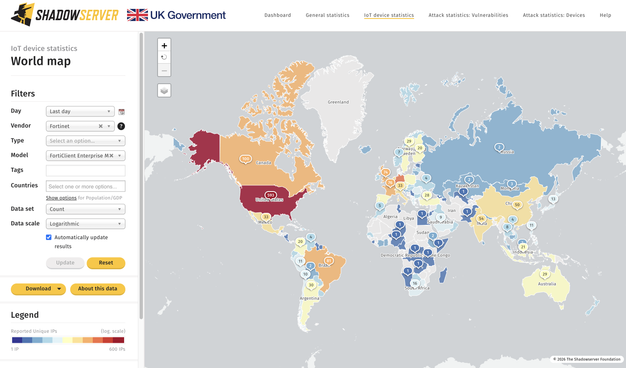
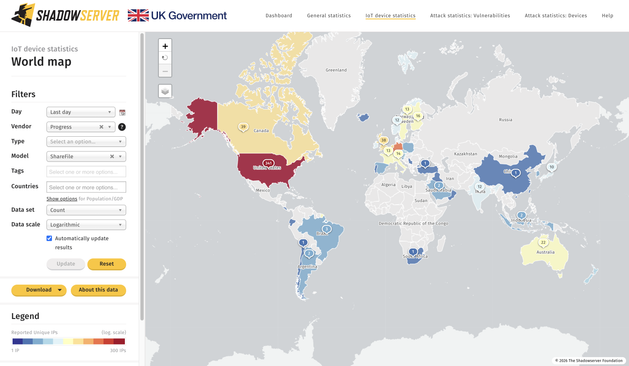
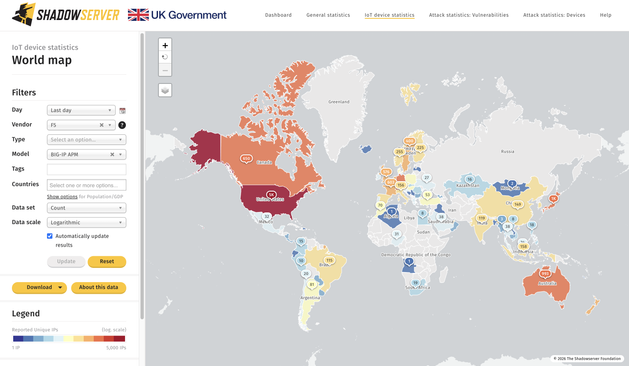
Dashboard World Map view: https://dashboard.shadowserver.org/statistics/combined/map/?date_range=1&map_type=std&source=http_vulnerable&source=http_vulnerable6&tag=cve-2025-48700%2B&data_set=count&scale=log&auto_update=on
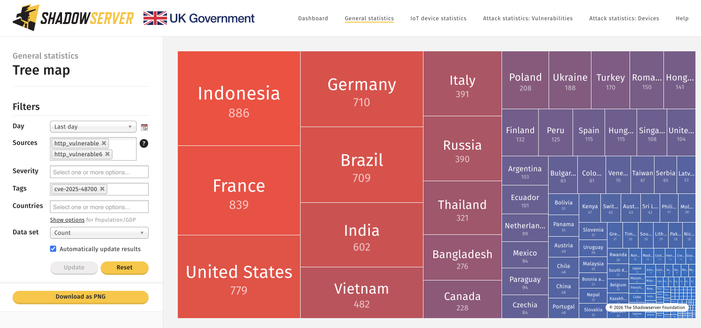
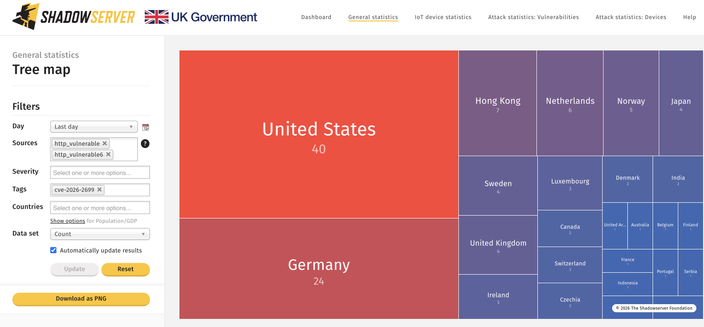
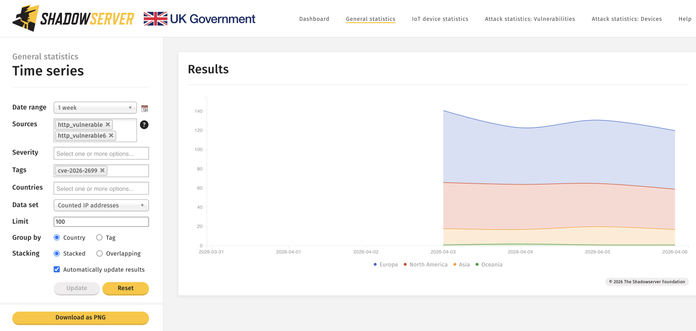
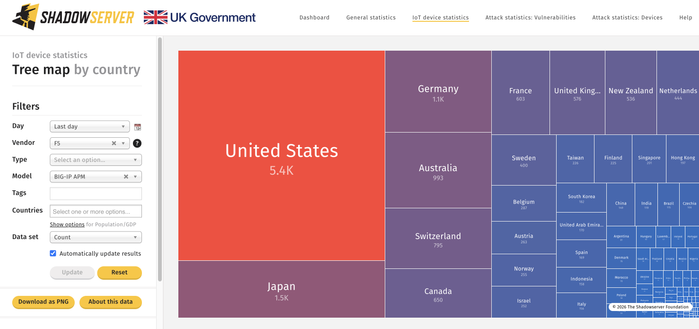
Dashboard Tree Map view: https://dashboard.shadowserver.org/statistics/combined/tree/?date_range=1&source=http_vulnerable&source=http_vulnerable6&tag=cve-2025-48700%2B&data_set=count&scale=log&auto_update=on