Ohne neue Linux-Root-Lücke wegen der das RZ die Häflte der Server abstellt, ist es inzwischen ja sonst auch gar kein richtiges Wochenende mehr.
"Logic bug in the Linux kernel's __ptrace_may_access() function"
👇
https://www.openwall.com/lists/oss-security/2026/05/15/2
Newest Linux kernel vulnerability mitigation:
# echo 2 > /proc/sys/kernel/yama/ptrace_scope
# echo 'kernel.yama.ptrace_scope=2' > /etc/sysctl.d/ssh-keysign-pwn.conf
On all deb systems you can install linux-vulnerability-mitigation from https://people.debian.org/~daniel/linux-vulnerability-mitigation/
Source: https://forgejo.debian.net/linux/linux-vulnerability-mitigation/src/branch/main/mitigations
#Linux #debian #Ubuntu #kernel #security #mitigation #sshkeysignpwn
Je me demande pourquoi toutes ces failles Linux sortent maintenant ?
https://www.phoronix.com/news/Linux-ssh-keysign-pwn
#linux #sécurité #faille #faillesécurité #dirty_frag #fragnesia #sshkeysignpwn
⚠️ 🤪 🔥 
Nouvelle vuln kernel Linux aujourd'hui : ssh-keysign-pwn 🔑
Pas une LPE cette fois, mais lecture de fichiers root en user non-privilégié :
• Clés privées SSH host (ecdsa/ed25519/rsa)
• /etc/shadow → crack offline
Le bug : ptrace_may_access() saute le check dumpable quand mm=NULL. Race window entre exit_mm() et exit_files(). Flaggé par Jann Horn en 2020... corrigé en 2026. 6 ans.
Confirmé sur : Debian 13, Ubuntu 22/24/26, Arch, CentOS, RPi OS. Pas de prérequis CONFIG spécifique donc cela semblerait bien plus universel que Fragnesia.
Patch mergé dans mainline par Linus aujourd'hui (31e62c2ebbfd), pas encore dans les kernels stables.
Pas de CVE assigné à ce stade.
👇
https://github.com/0xdeadbeefnetwork/ssh-keysign-pwn
"Six-Year-Old Linux Kernel Flaw Lets Unprivileged Users Read Root-Owned Files
"
⬇️
https://9to5linux.com/six-year-old-linux-kernel-flaw-lets-unprivileged-users-read-root-owned-files
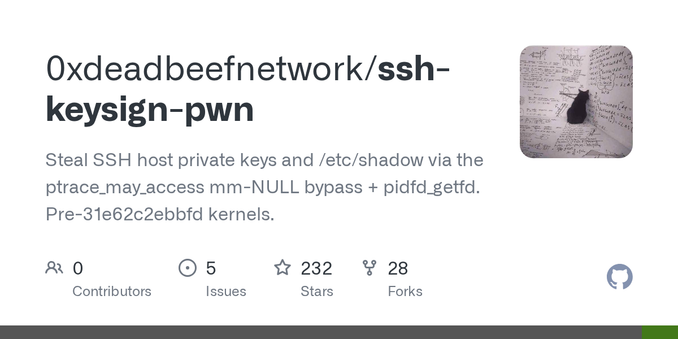
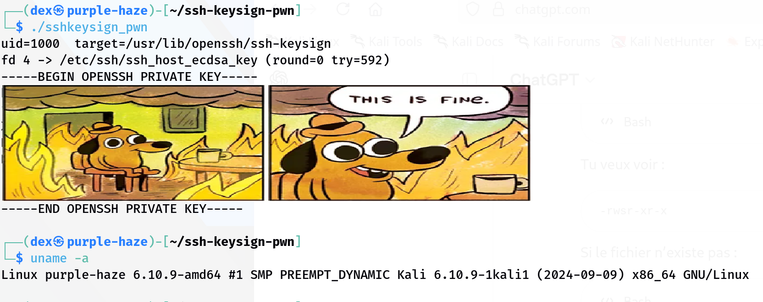
GitHub - 0xdeadbeefnetwork/ssh-keysign-pwn: Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels.
Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels. - 0xdeadbeefnetwork/ssh-keysign-pwn
Oh no, please don't tell me again that Linux is now insecure on the net?!
«Linux's Latest Vulnerability Allows Reading Root-Owned Files By Unprivileged Users»
⛓️💥 https://www.phoronix.com/news/Linux-ssh-keysign-pwn
⛓️💥 https://github.com/0xdeadbeefnetwork/ssh-keysign-pwn
#sshkeysignpwn #pwn #ssh #linux #0day #keysigning #sshkeys #itsecurity #itsec #itsecurity #zeroday

 decio
decio