On-Chip Light Systems Emerge Amidst Quantum Computing Claims
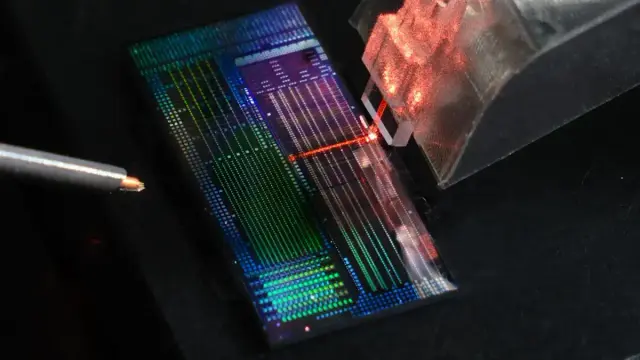
Monash University researchers in Melbourne have developed a new light-managing chip system. This technology could lead to faster computers and better communication.
#MonashUniversity, #LightChip, #Photonics, #QuantumComputing, #MelbourneTech
https://newsletter.tf/monash-university-new-light-chip-system/