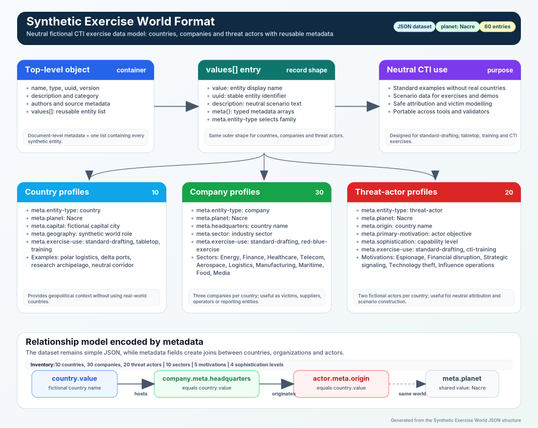
Synthetic Exercise World – Fictional dataset for cyber exercises and standards
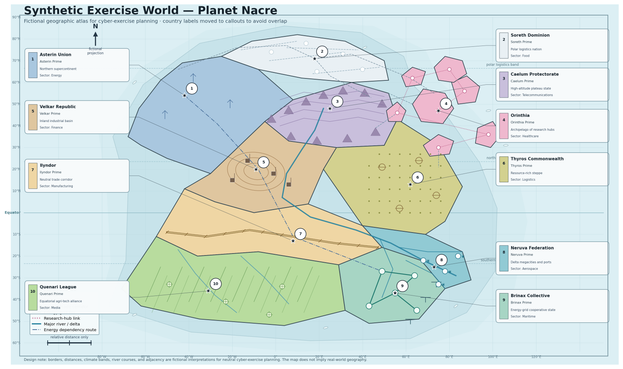
Synthetic Exercise World는 사이버 위협 인텔리전스(CTI) 훈련과 표준 문서 작성을 위한 중립적이고 재사용 가능한 가상 데이터셋을 제공한다. 이 데이터셋은 허구의 국가, 기업, 위협 행위자를 포함하여 실제 지정학적 상황이나 민감한 정보를 배제하고, 다양한 훈련 시나리오와 도구 간 상호운용성을 높인다. JSON 형식으로 제공되며 MISP 갤럭시 구조와 호환되어 기존 CTI 플랫폼에 쉽게 통합 가능하다. 이를 통해 국가 간, 부문 간 협업과 표준화가 용이해지고, 정치적 민감성 없이 현실적인 사이버 위협 시나리오를 설계할 수 있다.
GitHub - MISP/Synthetic-Exercise-World-Format: The Synthetic Exercise World Format provides fictional countries, companies, sectors, and threat actors with structured metadata for neutral CTI examples, exercises, interoperability tests, and standards documentation without referencing real-world sensitive entities.
The Synthetic Exercise World Format provides fictional countries, companies, sectors, and threat actors with structured metadata for neutral CTI examples, exercises, interoperability tests, and sta...
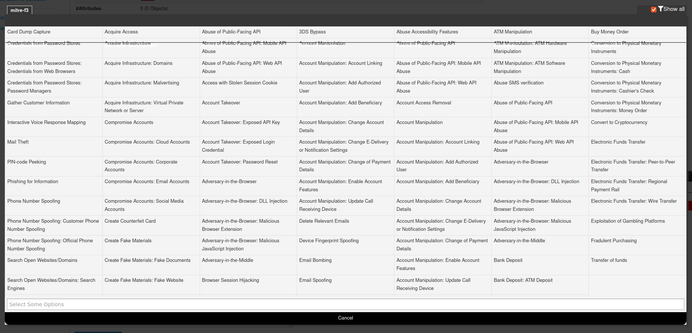
 misp-modules-cli
misp-modules-cli