In April of 1985 a writer for the Milwaukee Journal newspaper answered his phone only to find himself on a conference call with teenage hackers. These hackers told Eric K. Meyer, the journalist involved, details of his academic records from his high-school years, his electricity bill and his work history. All of this stemmed from an article Eric had written on a credit card fraud ring in Wisconsin. Also, important to note that the act of “doxing” or “doxxing” as we know it now did not have that name back in the 1980’s.
This blog is part of a series on the times that journalists have found themselves getting too close to the world of hackers, inadvertently becoming part of their own story. You can find some other entries in this series here and here.
Fraud has been a part of the history of hacking since day one in one form or another, whether it was to make free phone calls or to use stolen credit card numbers to purchase more computer equipment.
By 1985 small groups of kids across America were following ‘how to’ guides that they found on shady bulletin boards which gave them step by step instructions on finding card numbers and how to then order merchandise, hopefully without getting caught.
In order for a house to qualify as an inconspicuous drop spot, it must meet several requirements. It must look like a place where people could really live and be getting things sent through UPS to them. It must be a place that the owners will not 'visit' too regularly. It may have a 'FOR SALE' sign in front of it, but it is better if it doesn't. And most important of all, it must be a place that you can check up on often. Make sure you WRITE DOWN the address in a place where you will NOT forget it and where it will be readily accessible when you are ordering merchandise. (SEE STEP III)‘Credit Carding made easy’, by ‘David Lightman’, text file, March 28th, 1985
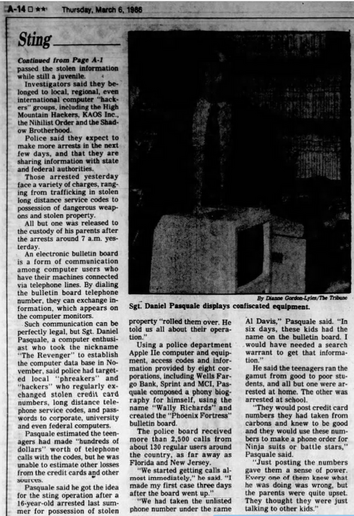
I wrote a couple of small blogs about the Nihilist Order, a carding group that made the news in 1986, but many others were busted before them. One such group of carders was in the small town of Waukesha, Wisconsin, when they got caught it became a brief news sensation.
‘Young hackers involved in major scam‘, UPI, The Bulletin, 30th April, 1985The article above details how six students at Waukesha’s North High School were caught using stolen credit cards to get “thousands of dollars worth of computer goods and services”, with the help of a “manual” on carding prepared by “Iceman, Leader of the Black Triangle”.
The “scheme involved purchasing thousands of dollars worth of computer-related equipment”, the kids had their carded computers and parts “sent to a mailbox rental service in Waukesha” which must have worked fine for them until “the Secret Service installed a video camera to monitor pickups from the box”.
The story initially broke in the Milwaukee Journal, which also carried some commentary from John Maxfield (aka ‘Cable Pair’), infamous 1980’s anti-hacker hacktivist, who was happy to name the BBS (‘The World of Cryton’) that he thought the accused kids had gotten their fraud manual from. Unfortunately the current owners of the Milwaukee Journal have decided to remove their newspapers archives that were online, so I can’t include that primary source and Iceman’s carding guide is also not archived anywhere I could find.
When this initial article was written by Eric K. Meyer and published in the Milwaukee Journal it got the attention of hackers elsewhere in the US. I wonder personally if this reaction was down to camaraderie, hatred by hackers across the U.S. of John Maxfield or because Eric was somehow disparaging of hackers in his original article.
‘Hacker Raids Private Files of Reporter‘, AP, Observer-Reporter, 10th May, 1985“A teen-age computer enthusiast has penetrated telephone and electric company records to compile a shockingly revealing dossier on me starting with only a telephone number”
Eric K. Meyer, Milwaukee Journal, May, 1985
Eric K. Meyer answered his home phone on a Sunday in May of 1985 to find himself on a conference call with a number of teenage hackers, one of whom identified as himself as “Master”. This hacker proceeded to outline to Eric certain private details of Eric’s life, what we would now call “doxing” (or “doxxing”).
I spoke to Eric via email and he told me “credit card numbers had been stolen and used to order computer components for delivery to a private mail drop.” He also clarified that “hacking had absolutely nothing to do with the theft of the credit card numbers. They were obtained via dumpster-diving at a Kohl’s Department Store in Waukesha, Wisconsin. In those days, most credit card sales slips had a sheet of carbon paper that copied the imprint information onto a receipt for the customer. Stores threw away the carbons… One sheet of carbon paper contained all the numbers needed to steal a card number.”
Kohl’s Department Store, Waukesha, WisconsinFrom the Associated Press’ reporting in ‘Hacker Raids Private Files of Reporter‘, we know that the hackers were able to “obtain a list of long distance telephone numbers the reporter had made” and “determine the amount of electricity used at Meyer’s home at peak and off-peak times and whether he had paid his bills on time”.
Armed with the details of long distance calls Eric had recently made, the hacker known as Master then “used the telephone numbers to obtain information from Meyer’s relatives, colleagues and acquaintances.” Eric Meyer recounts in the article that the hacker posed as “Dr. Richard Teller. vice president of the American Broadcasting Co. in Washington, D.C., and elicited) from those answering his calls background information for a prestigous national award in journalism that I was supposedly being considered for”.
‘Part-time workers gave hackers credit data’, UPI, The Telegraph-Herald, 1st May, 1985The 6 teenagers in Waukesha were caught and Eric K. Meyer got an interesting follow up article from the calls from hackers he received in the aftermath. Describing the calls in our email exchanges Eric wrote “some of the calls were conferences; some were individuals. They were vaguely threatening and wanting to portray themselves as far more powerful and ingenious than they were. Honestly, it struck me as typical teenage machismo.”
Eric told me that while the hackers “claimed they used computers to [retrieve his private details]”, some “further investigation revealed that the only computer usage involved looking up the customer service phone numbers of the utilities.” The hackers had in fact used “what they called “social engineering” — basically, the skills of a con artist — they were able to get details about my accounts over the phone”.
This is still how a lot of initial access to sensitive information is obtained by hackers to this day.
Many thanks to Eric for being willing to reply to my emails and help me research this blog.
#1980s #1985 #80s #BlackTriangle #CablePair #carded #carders #carding #careditCard #creditCard #doxing #doxxing #EricKMeyer #EricMeyer #fraud #hacker #hackers #hacking #history #Iceman #JohnMaxfield #Master #MilwaukeeJournal #newspaper #SecretService #Waukesha #Wisconsin