Hey everyone! It's been a bit quiet over the last 24 hours, but we still have some critical updates to cover, including a university email system compromise, an ongoing exploitation campaign targeting Cisco devices, and a significant arrest in the cybercrime world. Let's dive in:
University of Pennsylvania Hit by Politically Motivated Email Attack ⚠️
- The University of Pennsylvania is investigating a fraudulent and offensive email sent to thousands of current and former students from a compromised Graduate School of Education (GSE) address.
- The email contained criticisms related to affirmative action and threatened a data leak, mirroring similar attacks on other universities (Columbia, NYU, UMN) following the Supreme Court's ruling on race-based admissions.
- This incident highlights how politically motivated actors are leveraging cyber means, specifically email system compromises, to push agendas and potentially exfiltrate sensitive data. Organisations should bolster email security and incident response plans.
🗞️ The Record | https://therecord.media/upenn-hacker-email-affirmative
Ongoing BADCANDY Attacks Exploiting Cisco IOS XE Vulnerability 🛡️
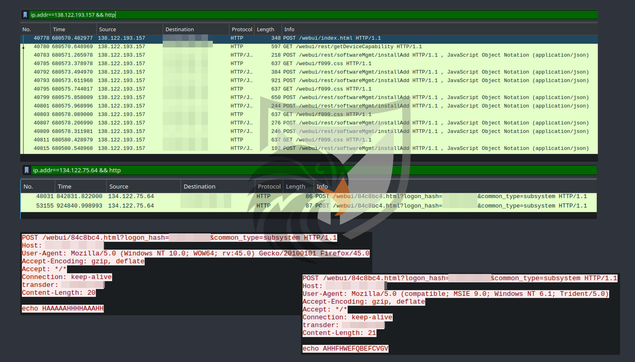
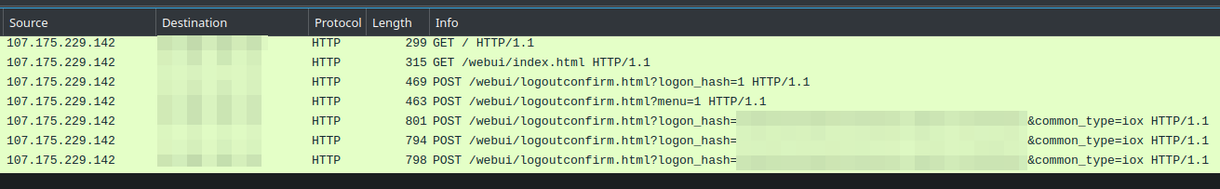
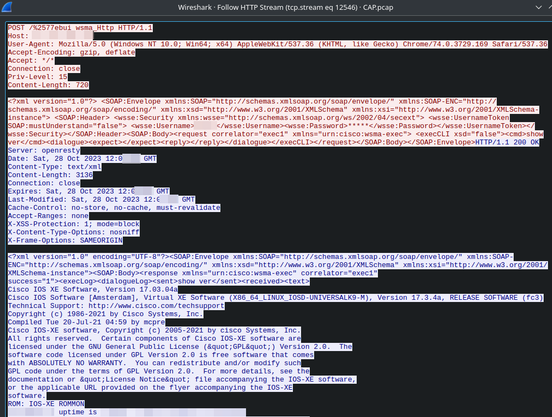
- The Australian Signals Directorate (ASD) has warned of persistent cyber attacks targeting unpatched Cisco IOS XE devices, exploiting the critical CVE-2023-20198 (CVSS 10.0) vulnerability.
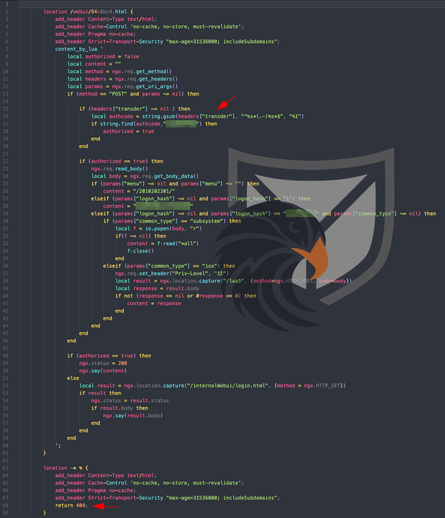
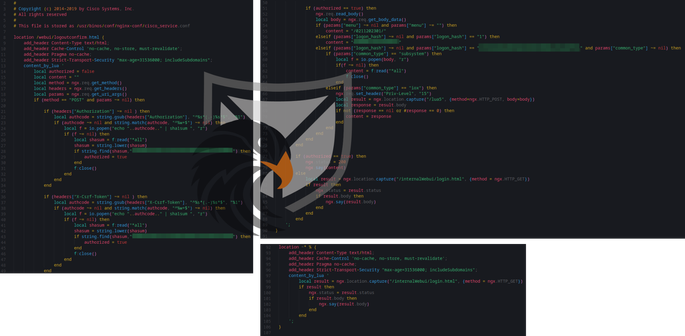
- Attackers are deploying a new, low-equity Lua-based web shell implant called BADCANDY, which allows them to create privileged accounts and seize control. While non-persistent, threat actors are re-infecting devices after reboots if they remain unpatched.
- Defenders must immediately patch Cisco IOS XE devices, limit public exposure of the web user interface, and review configurations for any rogue privilege 15 accounts (e.g., "cisco_tac_admin") or unknown tunnel interfaces.
📰 The Hacker News | https://thehackernews.com/2025/11/asd-warns-of-ongoing-badcandy-attacks.html
Alleged 764 Leader Arrested, Faces Life in Prison 🚨
- Federal law enforcement has arrested Baron Cain Martin, the alleged leader of 764, a violent extremist group, on 29 charges including providing material support to terrorists, child exploitation, cyberstalking, and murder.
- Martin, also known as "Convict," is accused of producing and distributing a guide on how to identify, groom, and extort vulnerable children, particularly those with mental health issues.
- This significant arrest is part of a broader crackdown on 764 and "The Com" – a global collective involved in financially motivated, sexual, and violent cybercrimes, underscoring the severe real-world impact of online criminal enterprises.
🤫 CyberScoop | https://cyberscoop.com/baron-cain-martin-764-leader-arrested-charged/
#CyberSecurity #ThreatIntelligence #Vulnerability #Cisco #IOSXE #BADCANDY #CyberAttack #IncidentResponse #Cybercrime #LawEnforcement #ChildExploitation #InfoSec
 Qiita - 人気の記事
Qiita - 人気の記事