Why a Locked Floppy Disk Could Be Safer Than a Modern Network
Photo by CCDBarcodeScanner, licensed CC BY-SA 4.0 via Wikimedia Commons.
Dear Cherubs, in the 1990s, office security had the elegance of a locked drawer and the threat model of a very determined coat thief. Floppy disks were the workhorses of the era, and Britannica notes they were popular from the 1970s until the late 1990s, made of flexible plastic coated with magnetic material. Before the internet became an everyday business utility, many workplaces were still mostly offline; Pew Research found that in 1995 only 14% of U.S. adults had internet access, and 42% had never heard of it.
THE LOCKED-BOX LOGIC
If your payroll files, drafts, and backups lived on removable media, the cleanest security move was physical control. Put the disks in a cabinet, lock the cabinet, and hope nobody on the third floor had a master key and a curious streak. It was a blunt system, but it worked because access was local, slow, and obvious. If someone needed a copy, they usually had to walk over, ask, sign something, and maybe endure a suspicious look from whoever guarded the supply room.
That is the part people forget when they romanticize the old days. The security was not magical; the attack surface was just tiny. To steal the data, someone usually had to be in the building, or at least within arm’s reach of the media. Annoyingly low-tech, yes. Also annoyingly effective.
MODERN SECURITY, NEW PROBLEMS
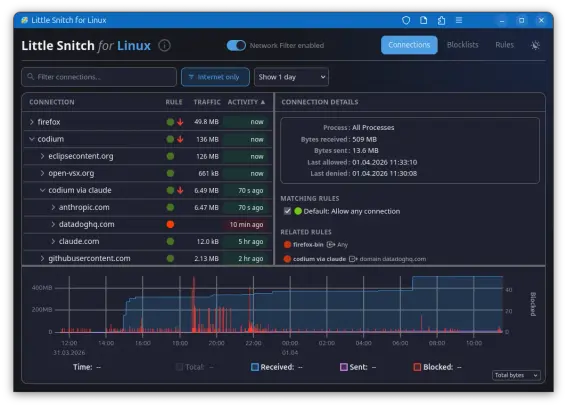
Once files moved onto networks and cloud systems, the game changed. NIST defines intrusion detection as monitoring events in a system or network for signs of possible incidents, and says intrusion prevention systems can also try to stop them. CISA says firewalls shield computers and networks from malicious or unnecessary traffic, while NIST says cryptography is used to protect sensitive digitized information during transmission and while in storage. In other words: the modern office traded one locked box for a whole stack of digital locks, alarms, and panic buttons.
Of course, the modern setup has its own virtues. Data can be backed up automatically, shared instantly, and protected with layered controls that the floppy-disk era never needed. NIST’s storage-encryption guidance still says organizations should physically secure devices and removable media, which is a polite way of saying: the box still matters, even when the box now lives in a server rack. Security did not become less important; it became more complicated, which is basically the same thing with extra meetings.
So yes, a locked plastic box full of floppies could be safer than a badly configured internet-facing system. But that is not because the past was wiser. It is because the past had fewer doors, fewer windows, and fewer strangers trying every handle on the planet at once. Security has always been a trade-off between convenience and control; we just used to do the math with keys instead of passwords.
Sources:
Britannica — https://www.britannica.com/technology/floppy-disk
Pew Research Center — https://www.pewresearch.org/internet/2014/02/27/part-1-how-the-internet-has-woven-itself-into-american-life/
NIST SP 800-94 — https://csrc.nist.gov/pubs/sp/800/94/final
CISA firewalls — https://www.cisa.gov/news-events/news/understanding-firewalls-home-and-small-office-use
NIST SP 800-175B Rev. 1 — https://csrc.nist.gov/pubs/sp/800/175/b/r1/final
NIST SP 800-111 — https://nvlpubs.nist.gov/nistpubs/Legacy/SP/nistspecialpublication800-111.pdf
Wikimedia Commons image page — https://commons.wikimedia.org/wiki/File:Floppy_Disk_HD.jpg
The Thisclaimer logo blends a classic warning symbol with a brain icon to represent critical thinking, curiosity, and thoughtful disclaimers.
#cybersecurity #dataSecurity #encryption #firewalls #floppyDisks #internetHistory #intrusionDetection #officeHistory #physicalSecurity #techNostalgia