Revision 709: HTTP/3 und WebTransport, mit Max Inden | Working Draft
Das war ein echt schöner Überblick über QUIC, HTTP/3, DoH und ECH. Auch immer mit einem "warum" mit schwingend.
Danke @mxinden 🙏
ECH Is Done, But Can We Make It Work?
https://www.feistyduck.com/newsletter/issue_136_ech_is_done_but_can_we_make_it_work
Ah #OpenSSL 4.0.0 est sorti la semaine dernière. Je note :
- Le support de SSLv3 dégage pour de bon
- Arrivée des salutations chiffrées (#ECH)
- Plus de crypto du turfu (post-quantique)
https://github.com/openssl/openssl/releases/tag/openssl-4.0.0
OpenSSL 4.0 Strengthens Privacy and Removes Legacy Protocols
OpenSSL 4.0.0 adds Encrypted Client Hello to protect browsing privacy, removes obsolete protocols, and introduces post-quantum cryptography.https://yoota.it/en/openssl-4-0-strengthens-privacy-and-removes-legacy-protocols/
OpenSSL 4.0: privacy rafforzata e addio ai protocolli vecchi
OpenSSL 4.0.0 arriva con il supporto a Encrypted Client Hello per proteggere la privacy nella navigazione, rimuove protocolli obsoleti e introduce crittografia post-quantum.https://yoota.it/openssl-4-0-privacy-rafforzata-e-addio-ai-protocolli-vecchi/
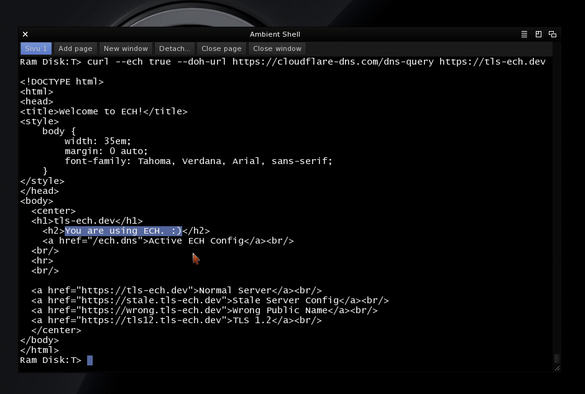
I pushed curl-rustls-8.19.0-3-x86_64.pkg.tar.zst to Arch Linux, with this version it's now possible to encrypt the TLS client hello:
curl-rustls -sSv --ech hard --doh-url='https://dns.mullvad.net/dns-query' 'https://defo.ie/ech-check.php'
Should display:
<p>SSL_ECH_OUTER_SNI: cover.defo.ie <br />
SSL_ECH_INNER_SNI: defo.ie <br />
The --doh-url is mandatory, otherwise curl won't query the `https` dns records (dig +short https defo.ie).
For opportunistic ECH use `--ech true`.
📢 RFC 9849 : Publication du standard TLS Encrypted Client Hello (ECH) par l'IETF
📝 ## 🌐 Contexte
Publié le 3 mars 2026 sur le datatracker de l'IETF (https://datatracker.ietf.org/doc/rfc9849/), ce document constitue la **RFC 9849**, un standard de la catégorie *Standa...
📖 cyberveille : https://cyberveille.ch/posts/2026-02-04-rfc-9849-publication-du-standard-tls-encrypted-client-hello-ech-par-l-ietf/
🌐 source : https://datatracker.ietf.org/doc/rfc9849/
#ECH #HPKE #Cyberveille