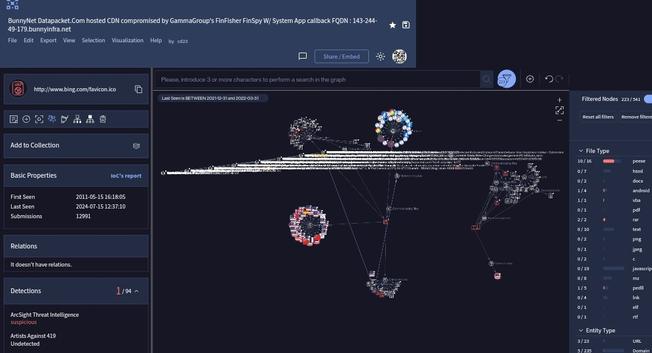
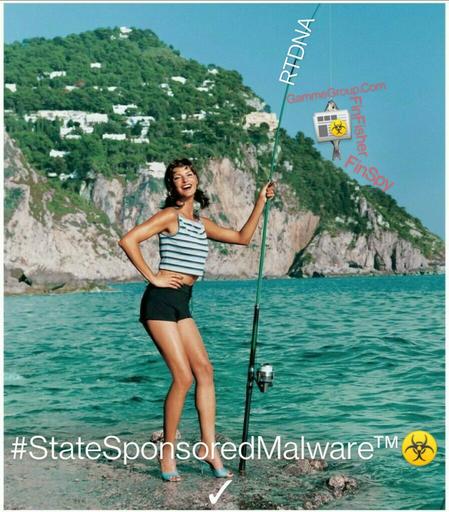
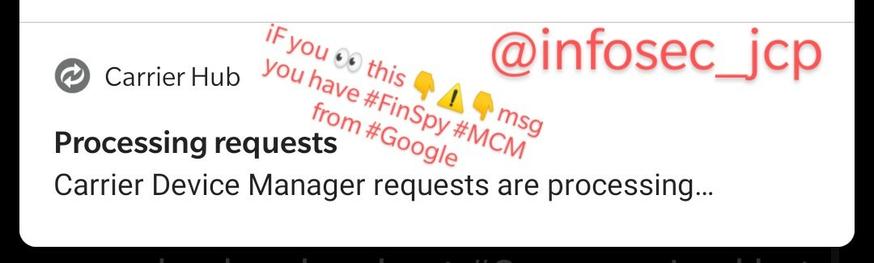
#GammaGroup #FinFisher #FinSpy #SystemApp callback caught #CALEA #malware #GreyMarket #investigations
💻🤝☣️🤝🤳 🎣🔍🧐
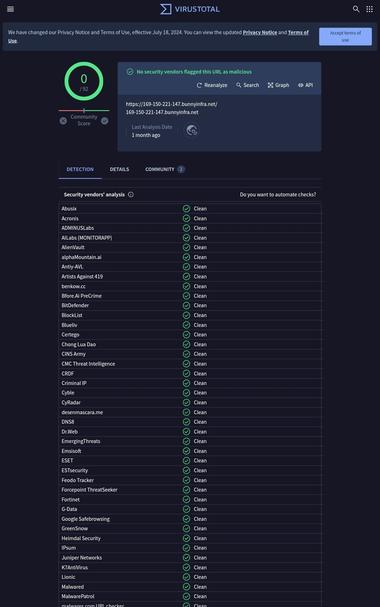
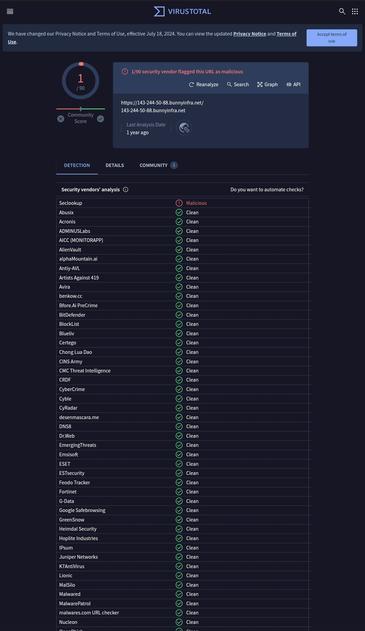
on #BunnyNet's CDN from #DataPacket
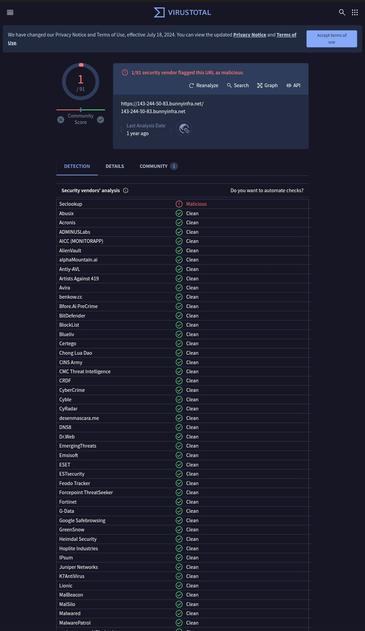
Interesting vectors... Quite the pointers this scan. Was scanned last 1yr ago. Showed up as malicious. Scans clean now except for the #malware found as a #GammaGroup shim caught nao. 🎣
Caught a bit o' Meta also in the callback graph. Huh.
#VirusTotal
https://www.virustotal.com/graph/embed/g7ee0dd48fe8e4dbbaf440955ee7bfbf57af12ca1c14543e08671f514fafb75be