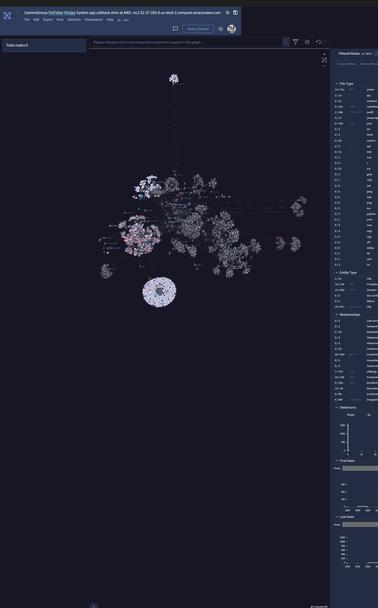
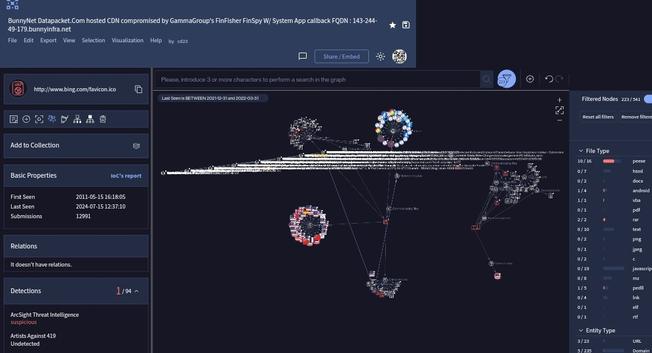
Historical list of #SystemApp callback to #FinFisher clients logged while on #InfoseceXchange that's good for #tcpdump correlation #investigations in #AMER on these IPs LARGE LIST hosting since November 2022ish for #Prosecutors to correlate.
#FinFisherCom🤝#EnemyOfTheInternet
#CALEA #greymarket #CALEAmalware 🔍🧐#infosec
¹
40.115.118.6
²
40.115.117.30
³ (fast .ly)
151.101.41.184
⁴
172.56.140.14
⁵
173.194.166.106
⁶
173.194.166.106
⁷
199.232.92.157
⁸ Twitter
104.244.42.66
⁹
151.101.190.110
¹⁰
138.91.55.166
¹¹
192.229.173.16
¹² Twitter
104.244.42.139
¹³
173.194.166.171
¹⁴
152.199.24.185
¹⁵
165.254.198.210
¹⁶ Fast .ly
151.101.42.2
¹⁷ Twitter
104.244.42.70
¹⁸ Fast .ly
151.101.40.193
¹⁹ Twitter
104.244.42.134
²⁰ Fast .ly
151.101.40.84
²¹
216.239.34.117
²²
104.26.2.192
²³
104.26.3.192
²⁴
172.67.72.251
²⁵
redirect.redhat.com
²⁶
192.229.210.163
²⁷
172.67.28.154
²⁸
104.18.10.19
²⁹
104.244.42.69
³⁰
944ellb0102-vip01.blackmesh.com
³¹
151.101.41.67
³² Fast .ly
151.101.40.81
³³
104.26.10.153
³⁴
151.101.41.188
³⁵
104.26.13.149
³⁶
104.26.12.149
³⁷
63.241.199.113
³⁸ Local ISP exploit try ip (private)
192.0.66.2
³⁹
162.159.153.4
⁴⁰
104.18.16.202
⁴¹
104.26.3.29
⁴²
104.26.2.29
⁴³ NYC Twitter
72.21.91.70
⁴⁴ Fast .ly
151.101.2.187
⁴⁵ Fast .ly
151.101.66.187
⁴⁶
13.86.218.255
⁴⁷
209.234.235.188
⁴⁸
104.26.15.185
⁴⁹
172.67.69.125
⁵⁰
52.239.139.228
⁵¹
104.17.83.11
⁵²
104.17.32.62
⁵³
104.244.42.130
⁵⁴
20.189.172.0
⁵⁵
172.67.222.28
⁵⁶
151.101.41.73
⁵⁷
13.86.218.248
⁵⁸
104.27.203.89
⁵⁹
104.16.13.194
⁶⁰
104.244.42.133
⁶¹
151.101.130.132
⁶²
172.67.73.80
⁶³
104.26.6.15
⁶⁴
104.22.33.123
⁶⁵
dns11.quad9.net
⁶⁶
104.244.42.198
⁶⁷
104.244.42.2
⁶⁸
104.244.43.131
⁶⁹
208.54.152.122
⁷⁰
208.54.150.98
⁷¹
52.236.40.36
⁷²
104.18.23.15
⁷³
104.26.1.5
⁷⁴
172.67.71.43
⁷⁵
199.232.93.184
⁷⁶
151.101.2.217
⁷⁷
199.232.92.81
⁷⁸
104.26.0.5
⁷⁹
151.101.130.217
⁸⁰
151.101.66.217
⁸¹
104.26.6.18
⁸²
104.18.22.15
⁸³
104.26.7.18
⁸⁴
104.21.78.132
⁸⁵
104.244.42.6
⁸⁶
199.232.92.200
⁸⁷
20.60.40.36
⁸⁸
52.245.40.74
⁸⁹
104.244.42.194
⁹⁰
199.232.94.110
⁹¹
172.67.72.57
⁹²
192.229.173.16
⁹³
104.244.42.193
⁹⁴
208.54.106.98
⁹⁵
104.244.42.65
⁹⁶
104.244.42.193
⁹⁷
151.101.67.52
⁹⁸
104.244.42.3
⁹⁹
151.101.67.52
¹⁰⁰
104.244.42.1
¹⁰¹
192.229.173.16
¹⁰²
151.101.40.159
¹⁰³
104.244.42.11
¹⁰⁴
152.199.24.185
¹⁰⁵
152.199.24.185
This is just # attaccc nodes for the past two years I have logged as #FinFisher shims/proxies/nodes. Every single one of these tried a MITM attaccc & multiple other OTS exploits. They were blocked and logged.
Cities:
¹
https://www.reddit.com/r/netzpolitik/comments/jax0e3/our_criminal_complaint_german_statemalware/
²
https://en.wikipedia.org/wiki/FinFisher
³
https://www.spiegel.de/netzwelt/netzpolitik/finfisher-ueberwachungssoftware-hersteller-ist-insolvent-a-399e29e2-a7ae-4966-8d26-fc3c4f92db64
⁴
https://netzpolitik.org/2022/nach-pfaendung-staatstrojaner-hersteller-finfisher-ist-geschlossen-und-bleibt-es-auch/
⁵
https://www.securityweek.com/german-authorities-seize-spyware-firm-finfishers-accounts/
⁶
https://www.bloomberg.com/news/articles/2022-03-28/spyware-vendor-finfisher-claims-insolvency-amid-investigation
#RTDNA #StateSponsoredMalware™ #SSM™ #malware