#cybersecurity #FinancialMarkets #IMF #CyberThreat #AI #Anthropic #Claude #Mythos
#cybersecurity #FinancialMarkets #IMF #CyberThreat #AI #Anthropic #Claude #Mythos
🔴 Windows Is Lying To Your Face Right Now
You clicked a link. The site looked real. Your credentials are already gone.
https://www.youtube.com/shorts/BP1RqnlnE8s
#cybersecurity #windowssecurity #networksecurity #cyberthreat #infosec #hacking #cve #vulnerability #threatintel #security
Windows Is Lying To Your Face Right Now #Shorts
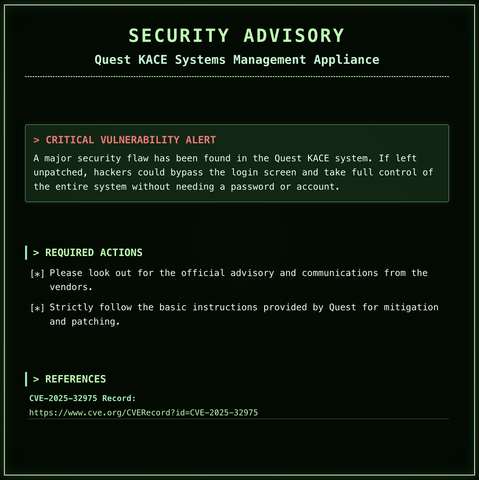
🔴 This Bug Lets Hackers Own Your Server
Hackers are exploiting this RIGHT NOW to take full control of your server.
https://www.youtube.com/shorts/jSZX8KC5OZk
#cybersecurity #Samsung #patchnow #infosec #cyberthreat #hacking #cve #vulnerability #threatintel #security
This Bug Lets Hackers Own Your Server #Shorts
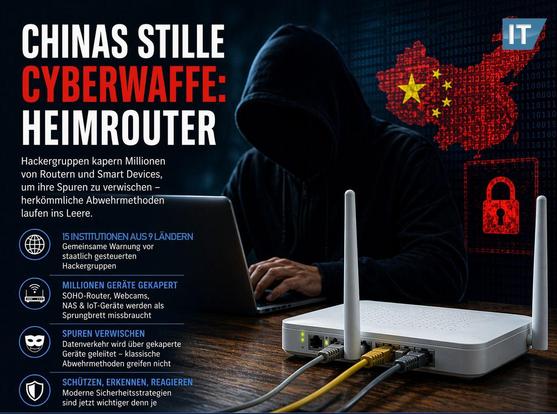
https://www.it-administrator.de/advisory-it-sicherheit-router-hacker-botnetz
#CyberSecurity #Hackergruppen #CyberThreat #ITSecurity #Netzwerksicherheit #Botnet #IoT #RouterSecurity #CyberAngriff #Cybercrime #Infosec #Datenschutz #ITNews #SecurityAwareness #StaySafeOnline
🚨 NEWS: Crittografia Post-Quantistica AES-128 Sicurezza Assicurata Contrariamente alle Credenze Diffuse
Ecco i punti chiave in breve:
💡 Nel panorama in rapida evoluzione della sicurezza informatica, un'errata convinzione persistente sta ostacolando i progressi fondamentali verso la preparazione all'era quantistica....
#sicurezzaDati. #crittografiaQuantistica #nIST #aES #cyberThreat
https://www.cve.org/CVERecord?id=CVE-2025-32975
#CyberSecurity #InfoSec #Vulnerability #QuestKACE #CVE2025_32975 #PatchManagement #SecurityAdvisory #ITSecurity #SysAdmin #CyberThreat
🧠 Formbook Daily Report
⬆️ Trend: rising (18%)
📊 15 new samples
🌐 55 C2 servers
Full analysis, IOCs, and hashes:
https://www.yazoul.net/malware/formbook/reports/2026-04-17
🧠 AsyncRAT Daily Report
⬆️ Trend: rising (34%)
📊 9 new samples
🌐 100 C2 servers
Full analysis, IOCs, and hashes:
https://www.yazoul.net/malware/async-rat/reports/2026-04-14
🧠 QuasarRAT Daily Report
⬆️ Trend: rising (22%)
📊 4 new samples
🌐 0 C2 servers
Full analysis, IOCs, and hashes:
https://www.yazoul.net/malware/quasar-rat/reports/2026-04-11
🧠 QuasarRAT Daily Report
⬆️ Trend: rising (158%)
📊 7 new samples
🌐 0 C2 servers
Full analysis, IOCs, and hashes:
https://www.yazoul.net/malware/quasar-rat/reports/2026-04-10