Hybrid Constructions: The Post-Quantum Safety Blanket
RE: https://dol.social/@dima/115969231949139332
Shoutout to Proton support - they helped me reset my Drive volume entirely.
The difference between RSA2048 and Curve25519 (ECC) on mobile is night and day. Loading is now instant, and the "thermal throttling" is gone.
Moral of the story: Modern crypto isn't just about security, it's about accessibility and efficiency.
Now my data is encrypted by my own key, and the system actually feels "functional" for the first time.
#Proton #GPG #Cryptography #ECC #Curve25519 #Infosec #TechDeepDive #Privacy #Blog #Thoughts #ProtonMail
Как я НЕ взломал ED25519
В этой статье будет описано, как один чересчур поверивший в себя программист пытался взломать один из фундаментальных алгоритмов криптографии. Эта статья признана огородить других от подобных попыток или наоборот заинтересовать новых смельчаков для подобной авантюры. Сначала я опишу суть алгоритма на простом коде, затем перечислю методы и идеи, которыми я пытался его взломать.
https://habr.com/ru/articles/939686/
#curve25519 #ed25519 #python #хакинг #криптография #эллиптические_кривые #исследования_в_ит #математика #edwards_curve #уязвимости
Gibt es eine leicht erfassbare und verständliche Übersicht, welche Kryptoalgorithmen, Schlüssellängen, etc. nach dem #StandDerTechnik verwenden sollte? Ich stelle mir da eine Liste vor, die ich einem Admin in die Hand drücken kann und er macht nix falsch.
Das @bsi erstellt zwar (schwer verdauliche) Empfehlungen. Aber diese schwiegen sich aus zu üblichen Verfahren wie #Curve25519, die in RFCs beschrieben sind. Bei #telestrust gabs das mal - ist in neuen Versionen aber herausgefallen. Und die Zusammenstellung der #NIST verweist oft auf andere Dokumente.
#InfoSec #Cryptographie #Kryptographie
#FollowerPower #PleaseBoost
@djb (Daniel J. Bernstein) tooted about a new blog post[1] he published. It's here:
https://blog.cr.yp.to/20250118-flight.html
It's interesting. He's a #mathematician and software guy that in more recent years has been known mostly for his work in #cryptography, #theoretical and #practical. You're probably using his #Curve25519 every day in your #communications.
I'm not a mathematician (by a long shot), but it's written in a pretty accessible manner - it's not #formulae and #turgid academic #prose.
The central point he's getting at, by my possibly-mistaken understanding of it, is that current "common sense" about when attacks against pre-quantum cryptography like #RSA (and therefore when post-quantum cryptography becomes critical) are badly mistaken - based on bad assumptions about how attacks work, how they're implemented, and on badly #extrapolating from those bad assumptions using logic that doesn't actually represent the way attacks are developed and become practical.
TL;DR is something along the lines of "#quantum cryptographic attacks against RSA will be practical sooner than most people think, and you should be deploying quantum-resistant cryptography now, not later".
It's worth reading if you're at all interested in #crypto and #security stuff.
He also mentions a project he's involved in that has been discussed separately, transparent post-quantum tunnelling for unmodified #server and #client #software. Link in post.
[1] Written more like a conference presentation, FWIW.
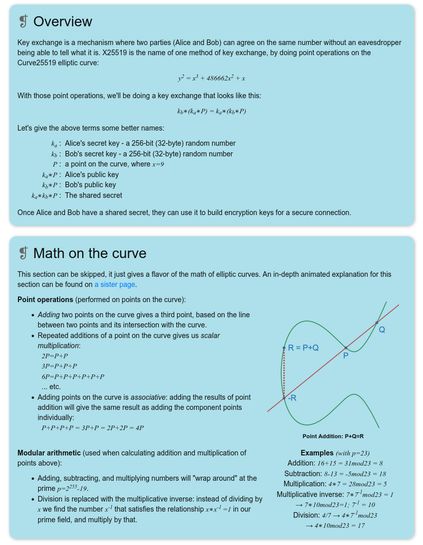
And this is all joined together into a page where an X25519 key exchange for TLS is explained: «Hands-on: X25519 Key Exchange: Let's exchange a secret to start a secure conversation.»
Excellent stuff anyone interested in #TLS and/or #ECC should always have handy. Wow!
6/6
#X25519 #KeyExchange #Curve25519
https://x25519.xargs.org/
Für #thunderbird gibts bei #nitrokey selbst eine Anleitung:
https://docs.nitrokey.com/de/nitrokey3/linux/openpgp-thunderbird.html?highlight=thunderbird
Coffee and elliptic curves
https://f.lapo.it/display/6a1cc041-1164-7767-4e2f-8f0061563271
Observation of today regarding Ed25519. I'm just trying to understand it on some level. Remember how did-keys have 44 significant "characters" in their base 58 encoding. This number 44 can be derived from 58**43 < 2**255 - 19 < 58**4, where 2**255 - 19 is the characteristic of the field the Curve25519 is considered over.
If my mathematical understanding is correct, there are always at most two points for a given y coordinate. So for the purposes of "representations" one can identify each point on Curve25519 with such a 44 character base 58 encoding.
Also please understand that figuring how numbers match is in no way mathematics. It just helps build a picture in my mind.
It’s 2023 and you’re designing a decentralised system based on public-key cryptography where a person’s identity(ies) are their public key(s).
Do you…
#cryptography #postQuantumCryptography #pqc #pq #ed25519 #curve25519 #x25519 #SmallWeb #Kitten