A high-severity flaw known as MongoBleed (CVE-2025-14847) is currently being exploited in the wild.
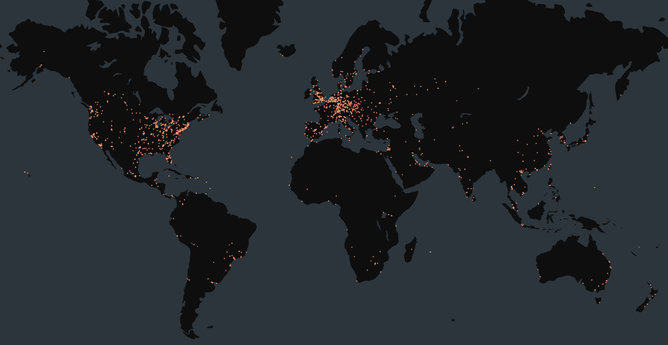
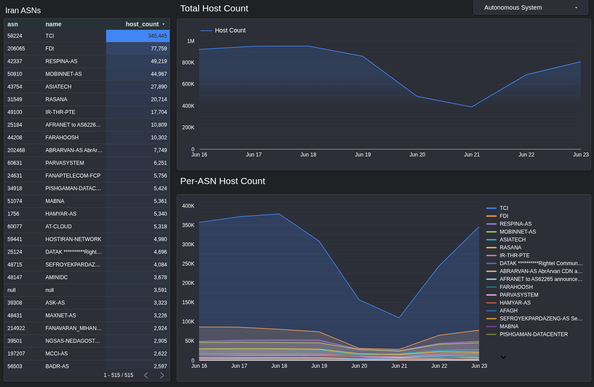
The scale is significant:
🔍 Wiz researchers have confirmed active exploitation.
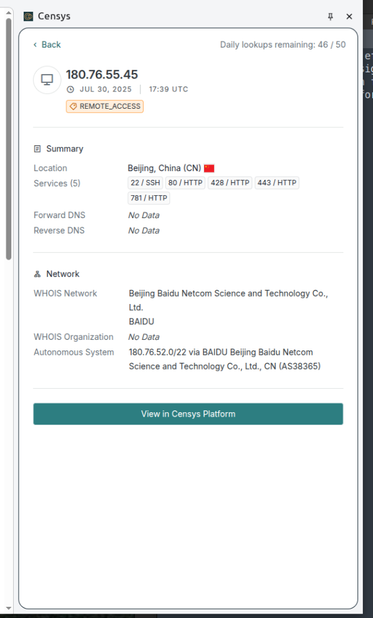
📊 Data from Shodan and Censys reveals between 87,000 and 100,000 potentially vulnerable MongoDB instances.
Read More: https://www.security.land/mongobleed-alert-cve-2025-14847-exploited-in-the-wild/
#SecurityLand #CyberSecurity #InfoSec #MongoDB #MongoBleed #DatabaseSecurity #Wiz #Shodan #Censys #CloudSecurity