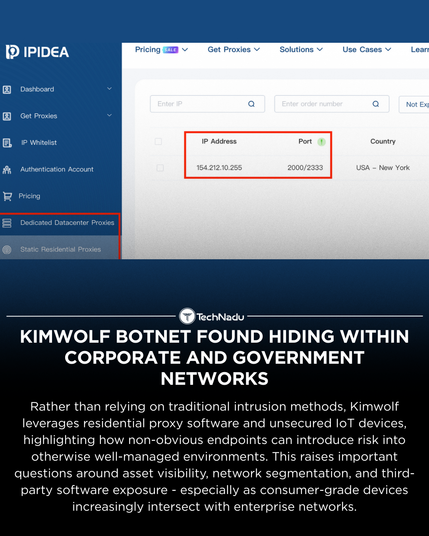
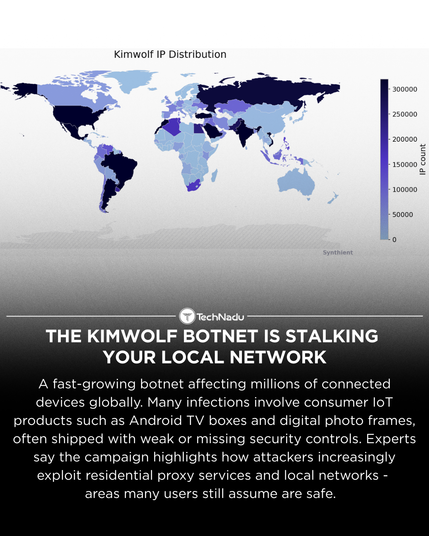
Analysis of the Kimwolf botnet highlights how residential proxy software and unsecured IoT devices can introduce lateral risk into enterprise, academic, and government networks.
Observed activity suggests that DNS queries and local scanning - not confirmed compromise - are often the first visible indicators, reinforcing the importance of segmentation, DNS controls, and asset awareness rather than assuming direct exploitation.
This case underscores how indirect exposure paths continue to challenge traditional security models.
Source: https://krebsonsecurity.com/2026/01/kimwolf-botnet-lurking-in-corporate-govt-networks/
Share your thoughts, and follow @technadu for neutral, research-driven infosec coverage.
#ThreatIntelligence #IoTSecurity #BotnetAnalysis #NetworkSegmentation #DNSecurity #Infosec #CyberDefense