📢 Void Dokkaebi migre InvisibleFerret vers des binaires Cython pour contourner les détections
📝 ## 🔍 Contexte
Publié le 22 mai 2026 par Kazuki Fujisawa (Trend Micro), cet article doc...
📖 cyberveille : https://cyberveille.ch/posts/2026-05-31-void-dokkaebi-migre-invisibleferret-vers-des-binaires-cython-pour-contourner-les-detections/
🌐 source : https://www.trendmicro.com/en_us/research/26/e/analyzing-void-dokkaebi-invisibleferret-malware.html
#AnyDesk #BeaverTail #Cyberveille
Void Dokkaebi migre InvisibleFerret vers des binaires Cython pour contourner les détections
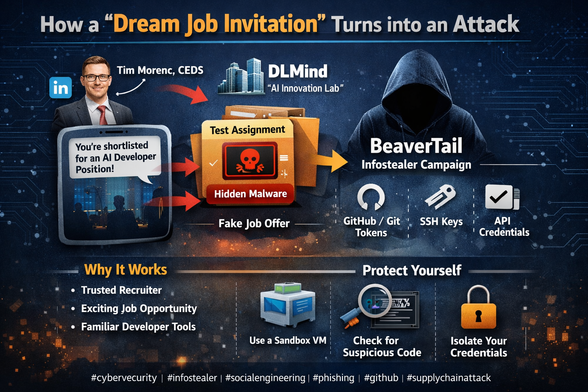
🔍 Contexte Publié le 22 mai 2026 par Kazuki Fujisawa (Trend Micro), cet article documente l’évolution technique du malware InvisibleFerret utilisé par Void Dokkaebi (alias Famous Chollima), un groupe d’intrusion aligné avec la Corée du Nord. 🎯 Acteur et cibles Void Dokkaebi cible systématiquement les développeurs de logiciels détenant des credentials de wallets cryptomonnaies, des clés de signature, et des accès aux pipelines CI/CD et infrastructures de production. Le vecteur initial historique repose sur de fausses offres d’emploi dans des entreprises crypto et IA, incitant les développeurs à cloner et exécuter des dépôts de code.