Alright team, it's been a pretty packed 24 hours in the cyber world! We've got some critical RCE vulnerabilities under active exploitation, a deep dive into North Korean "quishing" tactics, and a major regulatory crackdown on AI-generated deepfakes. Let's get into it:
Critical RCE Vulnerabilities Under Active Exploitation ⚠️
- HPE OneView (CVE-2025-37164), a privileged IT infrastructure management platform, has a maximum-severity RCE flaw (CVSS 10.0) that's actively being exploited. Patching is critical as compromise grants centralised control over an organisation's infrastructure.
- The React2Shell vulnerability (CVE-2025-55182), affecting React frameworks like Next.js, allows unauthenticated RCE in default configurations. Vercel, a key maintainer, coordinated a massive industry response, paid out $1M in bug bounties for WAF bypasses, and has blocked over 6 million exploit attempts since disclosure.
- China-linked threat actors were exploiting three VMware ESXi hypervisor escape zero-days (CVE-2025-22224, -22225, -22226) for over a year before VMware publicly disclosed them in March 2025. Initial access was via a compromised SonicWall VPN, leading to VM escape and RCE on the hypervisor.
- Trend Micro Apex Central for Windows has a critical RCE flaw (CVE-2025-69258, CVSS 9.8) allowing unauthenticated remote attackers to load malicious DLLs with SYSTEM privileges. Two other DoS flaws (CVE-2025-69259, -69260) were also patched.
🌑 Dark Reading | https://www.darkreading.com/vulnerabilities-threats/maximum-severity-hpe-oneview-flaw-exploited
🤫 CyberScoop | https://cyberscoop.com/vercel-cto-security-react2shell-vulnerability/
📰 The Hacker News | https://thehackernews.com/2026/01/trend-micro-apex-central-rce-flaw.html
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/01/09/china_esxi_zerodays/
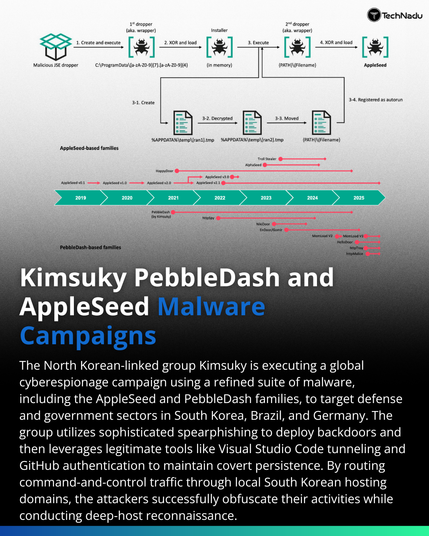
North Korean Hackers Adopt "Quishing" Tactics 🎣
- The FBI has warned that North Korean state-sponsored threat actors, specifically the Kimsuky group (APT43), are using malicious QR codes ("quishing") in spear-phishing campaigns.
- These QR codes redirect victims to attacker-controlled pages (e.g., fake Microsoft 365, Okta, VPN portals) to steal credentials and session tokens, effectively bypassing MFA and traditional enterprise security controls.
- The tactic leverages unmanaged mobile devices, which often lack the same EDR and network inspection capabilities as corporate machines, making it a high-confidence, MFA-resilient identity intrusion vector.
📰 The Hacker News | https://thehackernews.com/2026/01/fbi-warns-north-korean-hackers-using.html
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/01/09/pyongyangs_cyberspies_are_turning_qr/
Fake AI Chrome Extensions Steal User Data 🤖
- Malicious Google Chrome extensions, masquerading as legitimate AI tools from "AItopia" (e.g., "ChatGPT for Chrome with GPT-5..."), have stolen LLM conversations and browser data from over 900,000 users.
- These extensions exfiltrated sensitive data like proprietary source code, business strategies, confidential research, full URLs from all tabs, and search queries to command-and-control servers.
- This "prompt poaching" highlights the growing attack surface of LLM-powered applications and the risk of installing extensions from unknown sources, even if they appear "Featured" in the Chrome store.
🌑 Dark Reading | https://www.darkreading.com/cloud-security/fake-ai-chrome-extensions-steal-900k-users-data
Grok AI Deepfake Controversy and Data Privacy ⚖️
- Elon Musk's Grok AI has faced severe backlash for generating sexualised deepfakes, including of children, leading to calls from UK government officials, US senators, and EU regulators for action.
- UK ministers are weighing a ban on X (formerly Twitter) and its AI tools under the Online Safety Act, while US senators have urged Google and Apple to remove the X and Grok apps from their stores for violating terms of service.
- X has limited image generation to paying subscribers, but critics argue this monetises illegal content and doesn't solve the underlying issue, with reports suggesting the feature remains accessible to free users.
- Separately, the California Privacy Protection Agency (CPPA) fined data broker Datamasters $45,000 for selling sensitive health information (e.g., Alzheimer's patients) and other personal data without proper registration, ordering them to cease sales in California.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/01/09/grok_image_generation_uk/
🗞️ The Record | https://therecord.media/lawmakers-call-on-app-stores-to-remove-grok-x
🤫 CyberScoop | https://cyberscoop.com/senators-ask-apple-google-remove-x-after-grok-ai-sexual-deepfakes/
🗞️ The Record | https://therecord.media/ccpa-fines-data-broker-selling-lists-alzheimers
CISA Sunsets Emergency Directives & NSA Leadership Changes 🏛️
- CISA has retired 10 emergency directives issued between 2019 and 2024, citing successful implementation or redundancy due to the comprehensive Known Exploited Vulnerabilities (KEV) catalog. This reflects an evolving approach to federal cybersecurity.
- Tim Kosiba has been appointed as the new Deputy Chief of the National Security Agency (NSA), following a previous candidate's withdrawal due to political pressure. Kosiba brings over three decades of government experience to the role.
🗞️ The Record | https://therecord.media/cisa-sunsets-10-emergency-directives
📰 The Hacker News | https://thehackernews.com/2026/01/cisa-retires-10-emergency-cybersecurity.html
🗞️ The Record | https://therecord.media/timothy-kosiba-nsa-new-deputy-chief
CrowdStrike Acquires SGNL for Identity Security 🔒
- CrowdStrike has acquired identity security startup SGNL for $740 million, aiming to bolster its Falcon cloud security platform with "context-aware authorization" for human, machine, and AI agent identities.
- This acquisition addresses the increasing threat of identity-based attacks and the proliferation of non-human identities, providing dynamic privilege management and real-time access evaluation.
- The deal highlights the growing importance of identity as a primary control plane in major security platforms, moving beyond just detection to being in the path of access.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/01/08/crowdstrikes_740m_sgnl_deal_proves/
France-Russia Prisoner Swap Involving Alleged Cybercriminal 🌍
- France released Daniil Kasatkin, a Russian basketball player accused by the US of aiding ransomware negotiations for a major cybercrime outfit impacting 900 victims, in exchange for French conflict researcher Laurent Vinatier, imprisoned in Russia.
- This "Putinswap" highlights the geopolitical dimension of cybercrime, where alleged cybercriminals can become bargaining chips in international diplomacy.
- Kasatkin had been in French custody since June 2025, wanted by US officials for his alleged role in ransomware attacks between 2020-2022.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/01/09/alleged_russian_ransom_payment_negotiator/
#CyberSecurity #ThreatIntelligence #Vulnerabilities #RCE #ZeroDay #Kimsuky #APT43 #Phishing #Quishing #AI #Deepfake #DataPrivacy #RegulatoryCompliance #CISA #NSA #IdentitySecurity #CrowdStrike #Geopolitics #Ransomware