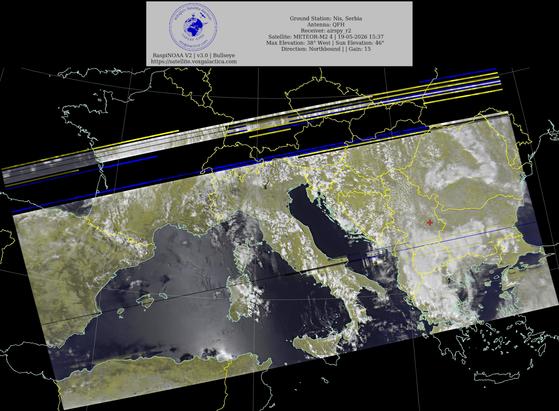
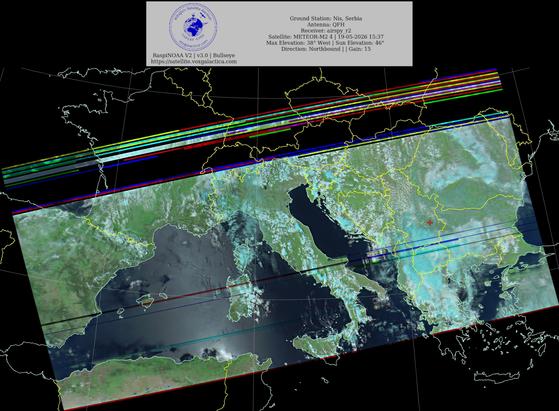
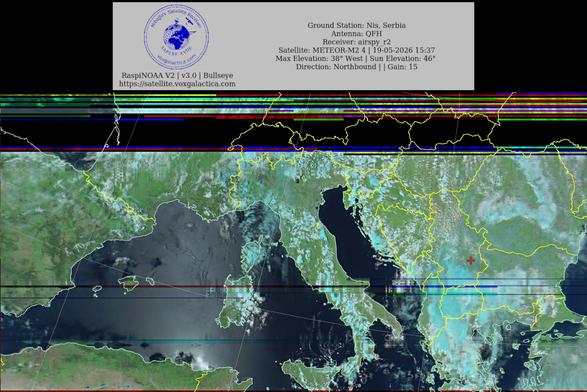
🇷🇸Ground Station: Nis, Serbia METEOR-M2 4 19-05-2026 15:22 CEST Max Elev: 38° W Sun Elevation: 46° Gain: 15 | Northbound
#NOAA #NOAA15 #NOAA18 #NOAA19 #MeteorM2_3 #MeteorM2_4 #weather #weathersats #APT #LRPT #wxtoimg #MeteorDemod #rtlsdr #gpredict #raspberrypi #RN2 #ISS
Malaysia has their own APT operation before Indonesia?
Damn
🔵 THREAT INTELLIGENCE
Weekly Threat Roundup: 2026-05-11 to 2026-05-17
Roundup | CRITICAL
CVEs: CVE-2026-20182, CVE-2026-42897, CVE-2026-42945
Cybersecurity roundup for 2026-05-11 to 2026-05-17. 3 CVE advisories, 3 breach reports, 1 threat news stories.
Full analysis:
https://www.yazoul.net/news/article/2026-w20-weekly-threat-roundup
🔵 THREAT INTELLIGENCE
Weekly Threat Roundup: 2026-05-11 to 2026-05-17
Roundup | CRITICAL
CVEs: CVE-2026-20182, CVE-2026-42897, CVE-2026-42945
Cybersecurity roundup for 2026-05-11 to 2026-05-17. 3 CVE advisories, 3 breach reports, 1 threat news stories.
Full analysis:
https://www.yazoul.net/news/article/2026-w20-weekly-threat-roundup
UAT-8616: il gruppo d’élite sfrutta il sesto zero-day Cisco SD-WAN e prende di mira governi europei e asiatici
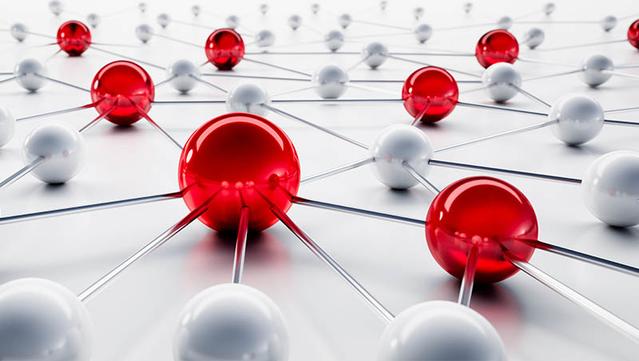
Un threat actor altamente sofisticato, UAT-8616, sfrutta CVE-2026-20182 — vulnerabilità critica CVSS 10.0 nel Cisco Catalyst SD-WAN — per compromettere organizzazioni governative, diplomatiche e della difesa in Europa e Asia Centrale. È la sesta zero-day sulla piattaforma SD-WAN nel 2026. La CISA ha aggiunto il CVE al catalogo KEV il 15 maggio.📰 Russian APT Turla Evolves Kazuar Backdoor into Stealthy P2P Botnet
🇷🇺 Russian APT Turla has upgraded its Kazuar backdoor into a modular P2P botnet. The new architecture enhances stealth and resilience, making it harder to detect and disrupt. The focus remains on long-term espionage. #Turla #APT #Kazuar #CyberSecur...
🌐 cyber[.]netsecops[.]io
📰 State-Sponsored Ransomware Blurs Lines, Increasingly Deployed as Proxy Weapon Against Critical Infrastructure
Nation-states are now using ransomware as a proxy weapon! ⚔️ Iran-aligned groups are targeting critical OT infrastructure to cause disruption while maintaining plausible deniability. #Ransomware #ThreatIntel #APT #OTsecurity
🌐 cyber[.]netsecops[.]io
Kazuar si evolve: Secret Blizzard (Turla) trasforma il suo backdoor storico in una botnet P2P modulare invisibile
Il gruppo russo Secret Blizzard (Turla/FSB) ha trasformato il malware Kazuar in una botnet peer-to-peer con tre moduli distinti (Kernel, Bridge, Worker) e 150 parametri di configurazione. La nuova architettura usa un sistema di elezione del leader per ridurre al minimo il traffico verso i server C2, rendendo il rilevamento estremamente difficile. Obiettivi: governi, ambasciate e settore difesa in Europa e Ucraina.