Since the start of Operation Epic Fury on February 28, 2026, Proofpoint researchers have observed heightened cyber activity against Middle East targets tied to the war. Our new blog shares examples of how the conflict in Iran is accelerating cyber espionage across the Middle East.
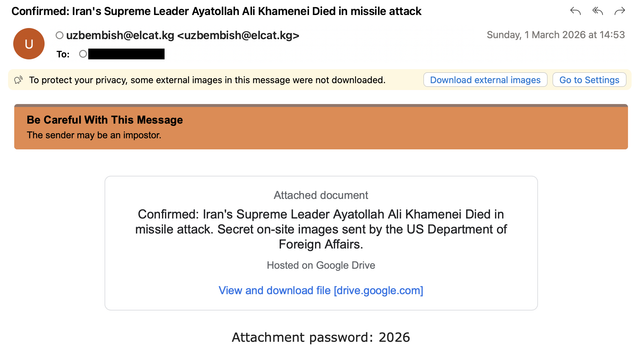
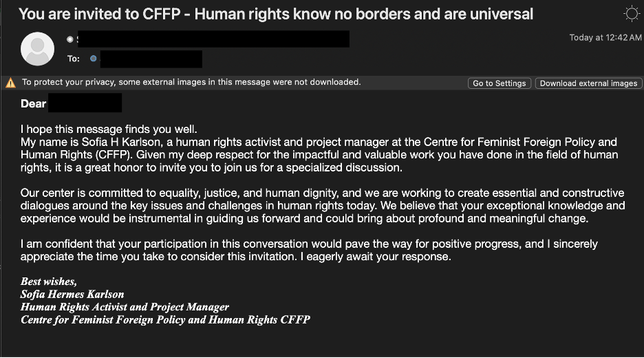
Iran-aligned #TA453 ( #CharmingKitten #APT42 ) recently attempted credential phishing against a U.S. thinktank, continuing its longstanding intelligence collection efforts. At the same time, multiple state-sponsored actors, including groups suspected to be linked to China, Belarus, Pakistan, and Hamas, are targeting Middle Eastern government entities using conflict-themed lures, often sent from compromised government or diplomatic accounts.
This reflects both opportunistic social engineering and a broader shift in intelligence collection priorities driven by the conflict.
View the full blog to see campaign examples observed by our researchers. We will continue monitoring the landscape and keep our customers and community informed as the situation evolves.