In the lead-up to #APNIC60, where Chief Technical Officer Leslie Daigle will give a keynote address, we’re publishing a series of articles that address regionally meaningful threats beyond the well-documented Chinese-origin attacks. Each case offers a different lens on the threat landscape—ranging from geopolitical motivations to financial disruption and targeted espionage. Our goal is to provide context, elevate regional perspectives, and set the stage for deeper discussion during the keynote.
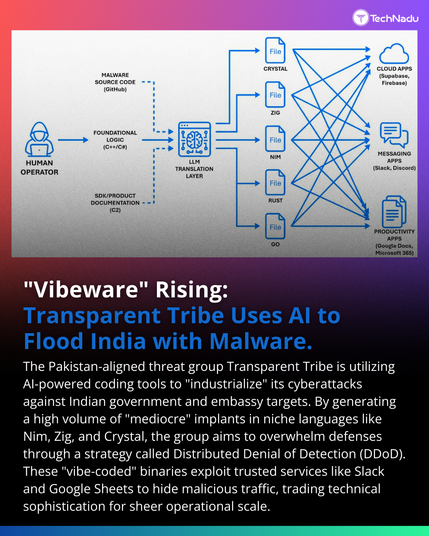
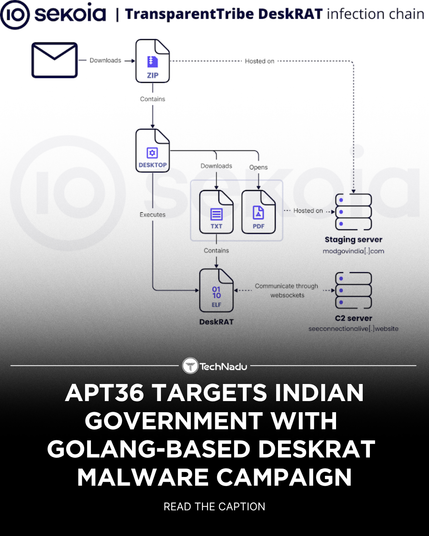
This is the first in that series, covering #APT36, a believed Pakistani state-aligned group that systematically exploits Internet service provider networks to launch cyber operations against Indian targets.
Between April and August 2025, AIDE captured 116,374 incidents on Indian sensors across 75 Autonomous System Numbers (ASNs) based in Pakistan.
The findings show how APT36 abused ISP infrastructure, deployed multi-architecture malware, and exploited routing security gaps at scale.
Read all about what we found, and stay tuned for the next installment.
https://globalcyberalliance.org/aide-data-apt36/
#threatintelligence #threatintel #cybersecurity #AIDE #research #malware #routingsecurity