Looks like #3cxpocalypse MAY actually be #3cx rainstorm … with much less damage than expected.
“Kaspersky has now found that the #hackers combed through the victims infected with its corrupted software to ultimately target fewer than 10 machines—at least as far as @Kaspersky could observe so far—and that they seemed to be focusing on #cryptocurrency firms with “surgical precision.””
https://www.wired.com/story/3cx-supply-chain-attack-north-korea-cryptocurrency-targets/
Originally posted by The Hacker News / @TheHackersNews: http://nitter.platypush.tech/TheHackersNews/status/1641737567715438592#m
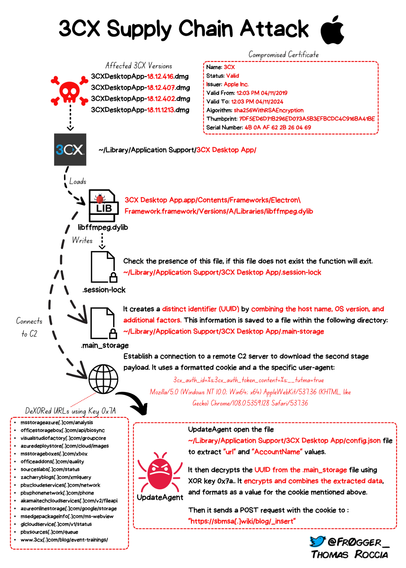
R to @TheHackersNews: The attack appears to have compromised 3CX's software build pipeline to distribute Windows and #macOS versions of the app package or poisoned an upstream dependency. The scale of the attack is currently unknown. 🔎
The Hacker News (@TheHackersNews)
The attack appears to have compromised 3CX's software build pipeline to distribute Windows and #macOS versions of the app package or poisoned an upstream dependency. The scale of the attack is currently unknown. 🔎 #cybersecurity #3CX #3CXpocalypse #3CXDesktopApp
🔍 If you are looking for a comprehensive overview of the current #3CX supply chain attack, I created a diagram that shows the attack flow for the Windows version! 💥
I'll update as soon as the analysis progresses. #cybersecurity #infosec #supplychainattack #3CXpocalypse
This is what we currently know about the #3cx compromise. Awesome job @JohnHammond @Embee_research and team from @huntress !
https://www.huntress.com/blog/3cx-voip-software-compromise-supply-chain-threats
botvrij.eu/data/feed-osin…
#3CXpocalypse #3CX