Codex plugins are packages for skills, mcps and prompts, adding descriptions, icon and tie them to distributed marketplaces to handle updates. r2mcp is now distributed as one.
Just run “make codex-plugin-install” and enjoy it in vscode, codex app and codex cli!
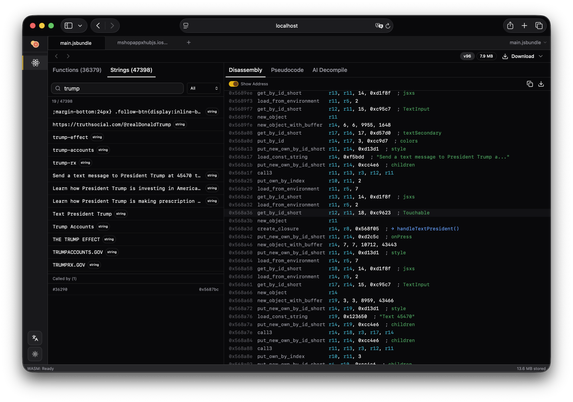
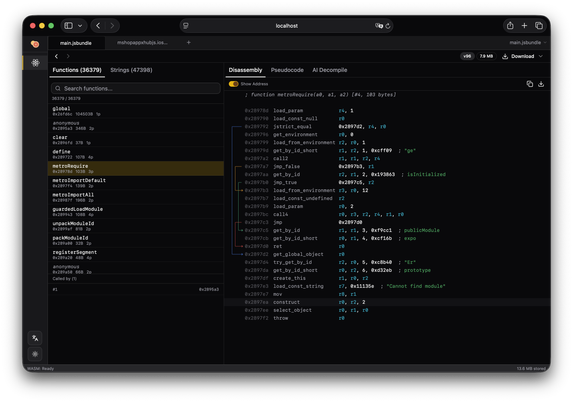
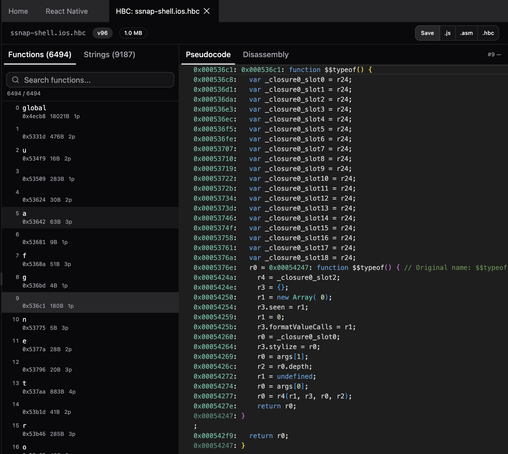
 radare
radare