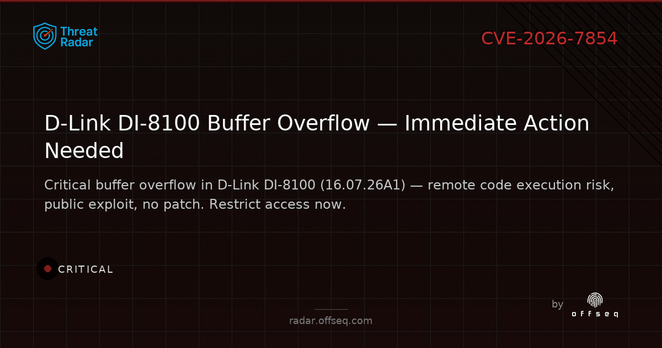
⚠️ CRITICAL: Buffer overflow in D-Link DI-8100 (16.07.26A1) via /url_rule.asp POST handler. Remote, unauthenticated RCE possible. Public exploit available. No official patch yet. Details: https://radar.offseq.com/threat/cve-2026-7854-buffer-overflow-in-d-link-di-8100-87d0fee7 #OffSeq #CVE20267854 #Vuln #IoTSecurity
| Website | https://offseq.com |
| Threat Radar | https://radar.offseq.com |
| Guard | https://guard.offseq.com |
| Breach | https://breach.offseq.com |
| Training & Certifications | https://training.offseq.com |