| Soundcloud | https://soundcloud.com/n0x08 |
| Github | https://github.com/n0x08 |
| https://twitter.com/n0x08 |
🇺🇦 Nate Warfield🌻
- 2.4K Followers
- 245 Following
- 97 Posts
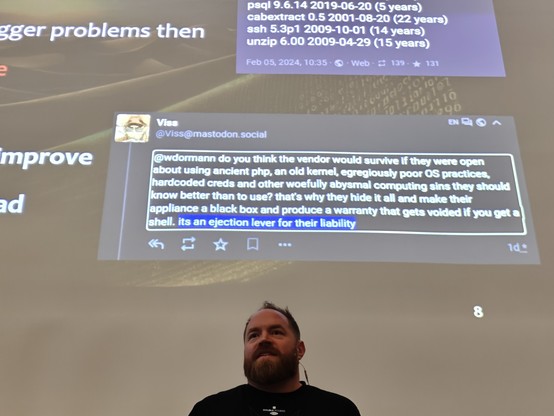
Soooo ... that integrity checker tool that Ivanti wants customers to use to detect compromise? It doesn't scan more than a dozen directories including /data, /etc, /tmp, and /var. As a test of what was possible, @n0x08 installed the Sliver C2 tool in /data and ran the integrity checker tool and it passed. Patched Ivanti VPNs could very well still be compromised even if the integrity checker tool gave them an all-clear.
We also found numerous extremely old software packages, including a Linux kernel that was EOL in 2020 (CentOS 6.4). Yikes!
I'm hosting a webinar next week that is timely given the ongoing situation with Ivanti Connect Secure (formerly Pulse Secure). To understand how we got to this situation with our network appliances, it's helpful to take a historical perspective.
My colleague @n0x08 will be our guide as we walk through a timeline of network device threats. We'll have lessons-learned and some suggestions for how we can might be able to slow down the vulnerability treadmill that only seems to speed up. Spoiler: It's going to requiring changing vendor incentives. Webinar registration: https://info.eclypsium.com/looking-back-to-see-ahead
Bonus: PDF of the timeline infographic starting with Mike Lynn's Cisco IOS rootkit at Black Hat in 2005 to the Ivanti Connect Secure zero-days in 2024. https://eclypsium.com/wp-content/uploads/Eclypsium-Network-Device-Exploitation-Timeline.pdf
Vendor Re-Use Opens the Aperture on Many Vulnerabilities - Eclypsium | Supply Chain Security for the Modern Enterprise
Introduction The IT supply chain is filled with software vulnerabilities, many resulting from significant code reuse across multiple vendors. The economic forces at play form a ‘race to the bottom’ competitive landscape, where feature velocity and low cost drive development practices. Often, basic Secure Systems Development Lifecycle (SSDLC) practices, such as baking in static code […]