| Soundcloud | https://soundcloud.com/n0x08 |
| Github | https://github.com/n0x08 |
| https://twitter.com/n0x08 |
🇺🇦 Nate Warfield🌻
- 2.4K Followers
- 245 Following
- 97 Posts
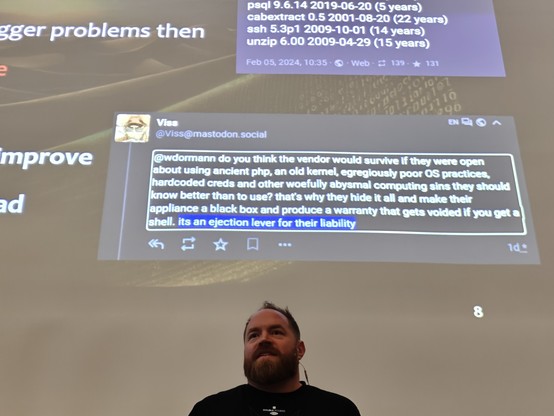
Soooo ... that integrity checker tool that Ivanti wants customers to use to detect compromise? It doesn't scan more than a dozen directories including /data, /etc, /tmp, and /var. As a test of what was possible, @n0x08 installed the Sliver C2 tool in /data and ran the integrity checker tool and it passed. Patched Ivanti VPNs could very well still be compromised even if the integrity checker tool gave them an all-clear.
We also found numerous extremely old software packages, including a Linux kernel that was EOL in 2020 (CentOS 6.4). Yikes!
I'm hosting a webinar next week that is timely given the ongoing situation with Ivanti Connect Secure (formerly Pulse Secure). To understand how we got to this situation with our network appliances, it's helpful to take a historical perspective.
My colleague @n0x08 will be our guide as we walk through a timeline of network device threats. We'll have lessons-learned and some suggestions for how we can might be able to slow down the vulnerability treadmill that only seems to speed up. Spoiler: It's going to requiring changing vendor incentives. Webinar registration: https://info.eclypsium.com/looking-back-to-see-ahead
Bonus: PDF of the timeline infographic starting with Mike Lynn's Cisco IOS rootkit at Black Hat in 2005 to the Ivanti Connect Secure zero-days in 2024. https://eclypsium.com/wp-content/uploads/Eclypsium-Network-Device-Exploitation-Timeline.pdf
Vendor Re-Use Opens the Aperture on Many Vulnerabilities - Eclypsium | Supply Chain Security for the Modern Enterprise
Introduction The IT supply chain is filled with software vulnerabilities, many resulting from significant code reuse across multiple vendors. The economic forces at play form a ‘race to the bottom’ competitive landscape, where feature velocity and low cost drive development practices. Often, basic Secure Systems Development Lifecycle (SSDLC) practices, such as baking in static code […]
https://infosec.exchange/@BleepingComputer/110119525019606098
The statistics in this report are not entirely accurate, due to a common misunderstanding in how the 'vuln:' search in @shodan works and I'll explain.
Searching by 'vuln:' requires a Small Business or higher license but anyone can see the vulns in the host detail page as a list on the lower right. The list is prefaced by the disclaimer "Note: the device may not be impacted by all of these issues. The vulnerabilities are implied based on the software and version."
This is because there is some CPE<->CVE magic happening behind the scenes. Only a small percentage of all vulnerabilities can be confirmed by Shodan via non-invasive tests - for obvious reasons they cannot spray exploit payloads across the internet.
They make these details available in the host raw data page. The key is the 'verified:' flag; below you can see the difference between CVE-2021-40438 (noted in the report) and MS17-010.
Many Apache vulns are config specific, require a specific module (like mod_proxy) be enabled, etc. In the case of some of the PHP vulns from the report, they also require specific conditions to be exploitable. While it's an interesting exercise to mine Shodan data in this way, exploitability of the top 4 CVEs in the report cannot be accurately determined via this method.
BleepingComputer (@[email protected])
Over 15 million publicly facing services are susceptible to at least one of the 896 vulnerabilities listed in CISA's KEV (known exploitable vulnerabilities) catalog. https://www.bleepingcomputer.com/news/security/15-million-public-facing-services-vulnerable-to-cisa-kev-flaws/
Yesterday my house sale closed. It took 1004 days to remove the cancer of my marriage from my life but it’s finally over & I get to start the next, best chapter of my life.
I’ve been through hell the last 3 years. The first month into the pandemic my neighbor somehow caught himself on fire; I put him out but he still died in the hospital. The smell of burning human you cannot forget. After that … some ugliness I won’t post online. Dad got cancer later that year. I hit rock bottom in 2021 & only by my strength of character am I still here. I had to come to terms with being in an abusive relationship; something that, as a man, we’re programmed to think doesn’t happen to us. I was married to Hanlon’s Razor & Ms. Hyde.
But during this time I quit smoking, finally got my mental health under control, I started to exercising this year and I’m under 200lbs (197 today!) for the first time in 15yrs. I’m a better dad, a better man, a better human. I have an amazing job at an awesome company where I literally get to do my favorite things - research & conference speaking - and get paid for it! And I work with the smartest people I’ve met in years. And I DJ’d at DC29, DC30 and will probably be back at DC31 this year 🤘
The next chapter of life has me buying another house for me & my kids, continuing to get fit, traveling the world dropping hacker knowledge & motivating the next generation to make the world a safer place. It’d be super cool to start dating but since I hate the apps, have my kids every weekend & 98% of my friends don’t live in Washington (so that whole “hey I have a friend you should meet” thing doesn’t work that well lol) … eh, I’m not spending cycles on it.
But the most important thing is I’m happy. Happier than I’ve been in easily 20 years. It feels cliche to use the whole “always darkest before the dawn” thing but the reason I’m sharing personal pain on social media is this:
Somewhere out there, someone is feeling like I did the last three years. It’s easy to think that those of us well known in the community figures must have it all figured out.
But we don’t. We’re humans, and humans are messy, ugly complicated beings. You’re not alone, and don’t be afraid to reach out for help. A few good friends helped me more than they’ll ever know & I’ll close with this.
Mental health is a silent killer. Being bipolar is a huge factor in substance abuse, as is depression. Don’t be afraid to talk about it & get help. Let’s not lose anymore friends for reasons that could have been avoided.
Looking for recommendations on conferences to submit to this year.
Already on the docket: TROOPERS, LABScon, BruCON, Ekoparty.
Preferably ones who cover T&E at some level since I don’t have MSFT money to send me everywhere anymore. Also I love international conferences.
Topic will be in the firmware security/networking space for context.