snackable 3/N on VexTrio and the WordPress hackers. This one's a bit geeky. One type of malware that led to VexTrio exclusively until late-Nov 2024 uses DNS TXT records to retrieve a redirection.
This is a tricky bugger and gives the malware actor an easy way to change things up if they are disrupted. The C2 domain (a DNS nameserver) isn't observed and the calls happen server side. The DNS TXT record malware was first observed by Sucuri/GoDaddy in 2023.
A compromised website makes a DNS TXT query that encodes the visitor's information and receives a redirection encoded in the response. When DNS queries to the C2 is blocked in the website's network, the visitor is protected -- we have had customers with compromised websites who still protected their users as we blocked the DNS query.
This malware is stubborn and is tricky to get rid of... there are also bots that come through regularly and update the compromised servers.
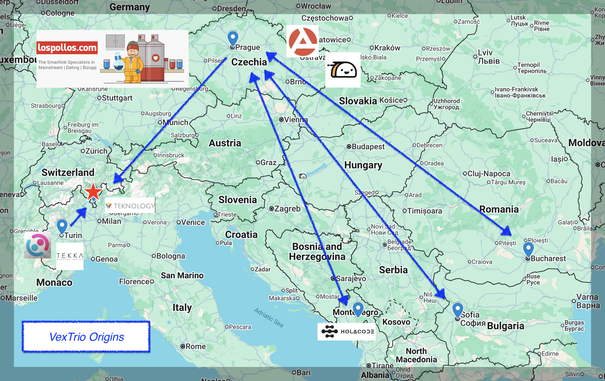
We used 4.5 million DNS queries over ~6 month period to understand how the C2 and redirect domains interrelated. What we found were two distinct clusters (this is the really geeky part) that indicate separate operations. Both use bulletproof hosting and/or Russian hosting, both were exclusively VexTrio, and both in late-November switched to the Help TDS. They used a few different paths to get to VexTrio's Los Pollos links.
One of these clusters had not been previously reported to our knowledge.
What you see in this image is a composite view. The C2 for each cluster are:
* data-cheklo[.]world, cndatalos[.]com, data-infox[.]com
* logs-web[.]com, airlogs[.]net, webdmonitor[.]io, cloudstats[.]net, etc.
webdmonitor[.]io is still active.
#dns #threatintel #cybercrime #cybersecurity #infosec #malware #scam #VexTrio #tds