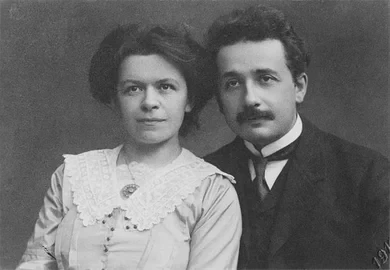
Mileva Marić Einstein was a physicist born in Serbia in 1875.
We remember her husband, Albert Einstein, as one of the most celebrated physicists of the 20th century, but I suspect most folks haven’t heard of her.
However, Albert & Mileva’s letters & other accounts suggest they worked together on his groundbreaking scientific contributions. They collaborated from the time they met in 1896 until their separation in 1914.
This is her story: https://blogs.scientificamerican.com/guest-blog/the-forgotten-life-of-einsteins-first-wife/?fbclid=IwAR2O8bwlDiEBgJLYbjKo-Kdy_3jhi7tvyCl2edzpzpI_pIcPv7iVOc1zC-E #science #history #HistoryRemix