#ESETresearch detected a recent intrusion at a University of Warsaw consistent with
#Interlock ransomware gang. Thanks to early warning from our experts and the university's swift cooperation, the attack was disrupted before encryptors could be deployed.
https://www.eset.com/pl/about/newsroom/press-releases/news/to-analitycy-eset-zidentyfikowali-atak-na-uniwersytet-warszawski/According to our investigation, the artifacts and infrastructure overlap with Interlock activity. We observed the use of
#NodeSnake RAT and Interlock RAT, both of which are referenced in CISA’s
#StopRansomware advisory.
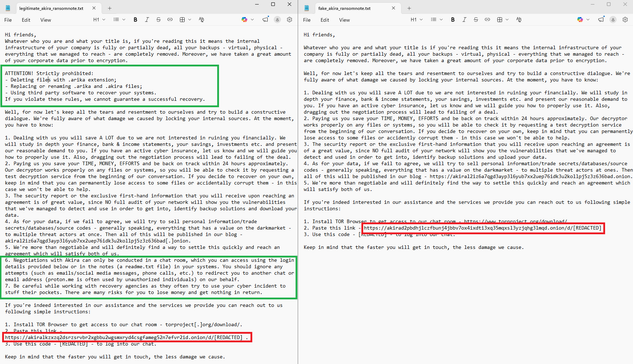
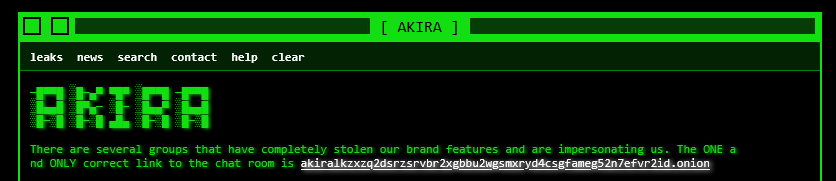
https://www.cisa.gov/sites/default/files/2025-07/aa25-203a-stopransomware-interlock-072225.pdfThe intrusion is a continuation of the threat actor’s campaign described in the April 2025 QorumCyber report, using an updated toolset. Our telemetry shows the actor targeted the education vertical in additional regions as well.
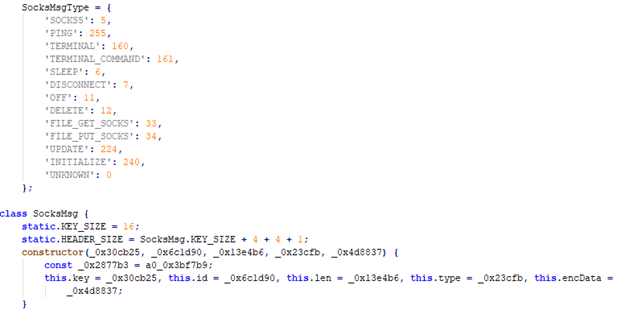
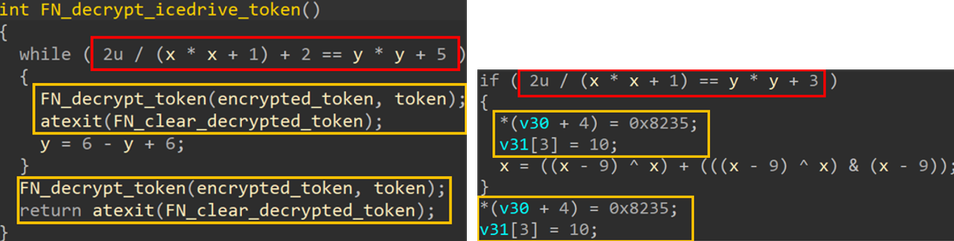
https://www.quorumcyber.com/wp-content/uploads/2025/04/20250416-Higher-Education-Sector-RAT-MP.pdf New in this campaign, we saw an updated, more-heavily-obfuscated NodeSnake RAT build. The updated version leverages WebSocket instead of the previously used HTTP. C&C infrastructure remains proxied mostly over Cloudflare’s *.trycloudflare[.]com infrastructure.
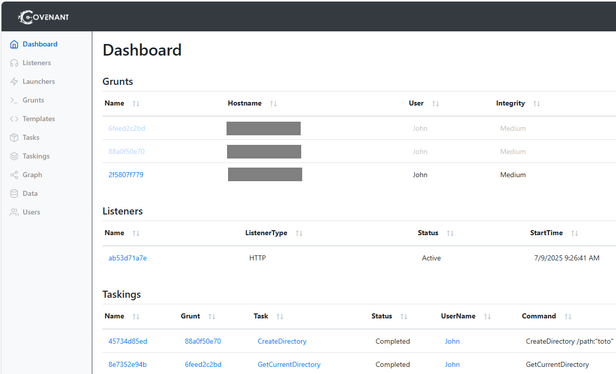
NodeSnake RAT was used to deliver its own updates and additional payloads including the legitimate tool AzCopy (for exfiltration), a PowerShell SystemBC proxy and a ConnectWise MSI installer (RMM).
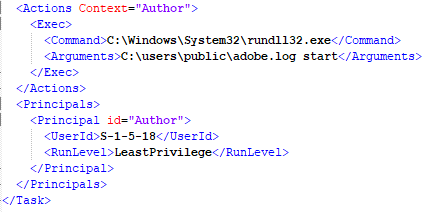
Interlock RAT (adobe.log) is executed via a scheduled task Microsoft\Windows\Defrag\ScheduledDefrg, masquerading as a defragmentation task.
IoCs:
Interlock RAT
CEB69DFDD768AA08B86F1D5628BD3A38C1FE8C1F
Interlock RAT C&Cs:
172.86.68[.]64
23.227.203[.]123
77.42.75[.]119
NodeSnake C&Cs:
deserve-coordinated-fairy-tier.trycloudflare[.]com
survey-tennessee-blind-corners.trycloudflare[.]com
dvd-diagnostic-oakland-signals.trycloudflare[.]com
practitioners-ons-boom-utc.trycloudflare[.]com
donnellykilbakk[.]cc
PowerShell SystemBC C&C:
91.99.97[.]247
ConnectWise C&C:
partyglacierhip[.]top