#ESETresearch has analyzed the resurgence of Sednit – one of the most long‑running Russia‑aligned APT groups – now using a modern toolkit built around paired implants, BeardShell and Covenant, each using a different cloud provider for resilience. https://www.welivesecurity.com/en/eset-research/sednit-reloaded-back-trenches/
ESET researchers tied Sednit’s advanced implant team reboot to a 2024 case in Ukraine, where SlimAgent emerged – a keylogger built on the codebase of the infamous Xagent, Sednit’s flagship 2010-era backdoor.
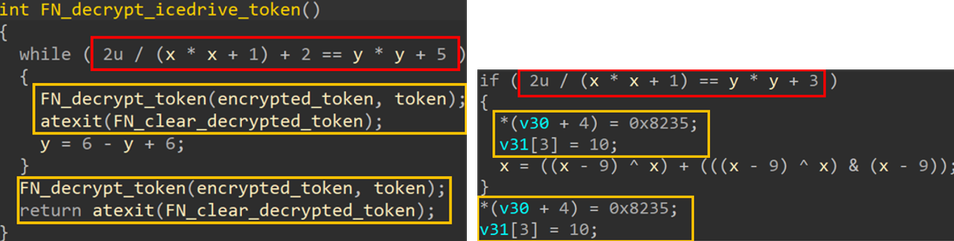
Sednit also deployed BeardShell, an implant that executes PowerShell commands via a legitimate cloud service and uses a distinctive obfuscation technique also found in Xtunnel, Sednit’s network pivoting tool from the 2010s.
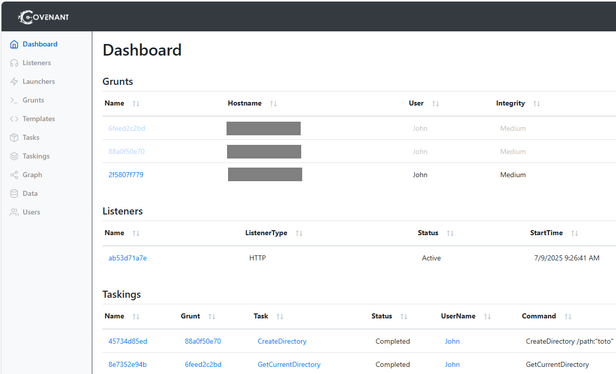
Across 2025–2026, Sednit paired BeardShell with Covenant, the final block of its modern toolkit – a heavily reworked open-source implant built for long‑term espionage with a new protocol riding on another legitimate cloud provider.
Detailed analysis of Sednit’s modern toolkits is available at https://www.welivesecurity.com/en/eset-research/sednit-reloaded-back-trenches/
ESET researchers tied Sednit’s advanced implant team reboot to a 2024 case in Ukraine, where SlimAgent emerged – a keylogger built on the codebase of the infamous Xagent, Sednit’s flagship 2010-era backdoor.
Sednit also deployed BeardShell, an implant that executes PowerShell commands via a legitimate cloud service and uses a distinctive obfuscation technique also found in Xtunnel, Sednit’s network pivoting tool from the 2010s.
Across 2025–2026, Sednit paired BeardShell with Covenant, the final block of its modern toolkit – a heavily reworked open-source implant built for long‑term espionage with a new protocol riding on another legitimate cloud provider.
Detailed analysis of Sednit’s modern toolkits is available at https://www.welivesecurity.com/en/eset-research/sednit-reloaded-back-trenches/