This post isn’t about what you think it is, so take a moment to read the POST, not just the PICTURE, before replying.
The picture of trikcode’s post says, literally, quoted with it’s bad grammar and syntax unmodified:
“the generation that refused to accept cookies.
is now giving AI access to their desktops, files, and bank accounts.”
This post isn’t about AI.
This post isn’t about privacy.
This post isn’t about incorrect grammar and syntax.
So, what am I posting about?
The evolution of language. And how we must embrace it.
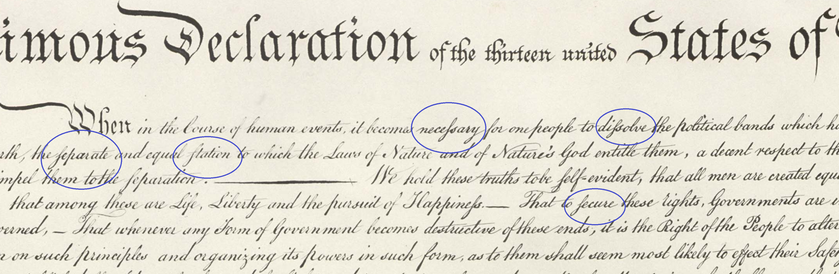
The grammar, syntax, spelling, and even the alphabet, of American English in the 1700’s doesn’t apply today. We don’t even write the letter “s” the same way our predecessors did. (Refer to the closeup picture of the Declaration of Independence).
Dictionaries list some words as “archaic” or “obsolete.” And new words are added to the dictionary because they become common and are well-understood.
Capitalization has changed over the centuries. In fact, there was a time when there weren’t upper-case and lower-case letters; there were just letters.
In the early days of the Internet, and in the early days of text messaging (these two time periods are not identical, BTW), I was dismissive of incorrect grammar, newly developed acronyms, lack of punctuation, and so forth.
But. Today. We can now see that these changes are consistent with long-understood and well-articulated principles of language development and morphology.
Such changes don’t happen overnight. Changes to language often occur first in slang and common usage before being accepted into business or formal communications. Also, changes in spoken language and changes in written language occur on two different tracks, and don’t always mirror each other.
In addition to linguistic changes in online written communications, I must at least briefly mention changes to verbal, oral communications that are simultaneously occurring because of the globalization of the English language. For example, in the USA, we traditionally put adjectives before nouns. We say, “cold water,” whereas in many other languages, the noun comes before the adjective. In Spanish, we say, “agua fría,” which in direct English translation would be “water cold.” We’re also not used to hearing the verb at the end of the sentence, unless we’re watching Yoda in Star Wars (“Try you must”), or hearing the verb at the beginning of the sentence unless we’re watching Mr. Miyagi in Karate Kid (“Is no defense”).
It is now common to read technical papers written in English by subject matter experts whose first language is not English. These articles, white papers, technical manuals, textbooks, and blogs contain sentence structures that sound odd to people who have grown up knowing only one language, and yet – AND YET – we completely understand the meaning of the “strangely organized” words.
Now we come to my point.
It is no longer appropriate to criticize differences in written or spoken language, unless it fails to communicate.
Languages evolve, in every way: alphabet, grammar, syntax, words, spelling.
If someone expresses an idea, and you understand the idea, their communication is perfect.
And if you don’t understand what they’re trying to communicate, don’t be too quick to judge. The problem may be on your end.