Amazing: #Debian is now shipping reproducible packages 💪
https://lists.debian.org/debian-devel-announce/2026/05/msg00001.html
Thanks to everyone who helped make this happen!
See https://reproducible-builds.org/ if you are not familiar with the topic
| Website | https://daniel.roe.ch |
| GitHub | https://github.com/droe |
Amazing: #Debian is now shipping reproducible packages 💪
https://lists.debian.org/debian-devel-announce/2026/05/msg00001.html
Thanks to everyone who helped make this happen!
See https://reproducible-builds.org/ if you are not familiar with the topic
A secret diplomatic letter written in 1498 once carried sensitive intelligence about England & Scotland to the Spanish court. More than five centuries later, historians from the University of Toronto have decoded its cipher and produced the most accurate version of the text yet.
Cryptographers, take note, we need to re-introduce non-injective permutations! </joke>
"Ayala sometimes used multiple symbols for the same letter, making the text even more difficult to decode.”
https://www.medievalists.net/2026/04/secret-letter-detailing-late-medieval-britain-fully-decoded/
#QEMU 11.0 is out! And with it an exciting feature I was working on: Support for #nitroenclaves. Yes, you can now launch your enclave via -kernel directly in QEMU 😁
NEW: Researchers have identified extensive spying campaigns abusing well-known weaknesses in the global cellphone infrastructure to track and locate targets.
Two (unnamed for now) surveillance vendors, whose customers are likely government agencies, were allegedly behind these spy campaigns.
The research exposes an industry that remains still largely in the shadows, armed with tech that can track people without the need to use spyware such as Pegasus.
A pretty significant change in resolver behavior is proceeding:
"[...] BIND 9 is switching to a parent-centric model of delegations. [...] The NS records in the child domain will be treated as normal DNS records and returned as authoritative data, but they will no longer overwrite the delegation data for the domain."
https://lists.isc.org/pipermail/bind-users/2026-April/110552.html
So much of what you may have learned about how #DNS works around the turn of the century is now out of date.
Getting serious ADHD and building software nobody asked.
checksec for Mach-O
https://github.com/ChiChou/macchk
⚠️ Warning: vibe coded
We publish a major Citizen Lab report on Webloc, an ad-based mass surveillance system that monitors the movements and personal characteristics of hundreds of millions people globally based on data obtained from mobile apps and digital advertising.
Customers include ICE, El Salvador and Hungary.
Our research shows that ad-based surveillance is now used by military, intelligence and law enforcement agencies down to local police in several countries.
Full report here:
https://citizenlab.ca/research/analysis-of-penlinks-ad-based-geolocation-surveillance-tech/
If you're following the situation in Iran, this one is of interest to you.
Today, we're publishing a story that I find very important for many reasons.
We can prove how the regime in Iran is using facial recognition software to surveil its citizens. We have obtained videos showing the software in a live-scenario, at metro stations in Teheran. We have contracts, and we have had a look at the code, built by the Russian company Ntechlab whose algorithms are deemed to be best-in class.
We spoke with a dozen people who know the regime, either because they had to flee after being imprisoned or from a technical point of view.
All of this, and more, you can find in our reporting, #EyesOfIran. Here are the links:
Forbidden Stories: https://forbiddenstories.org/iran-regime-monitors-citizens/
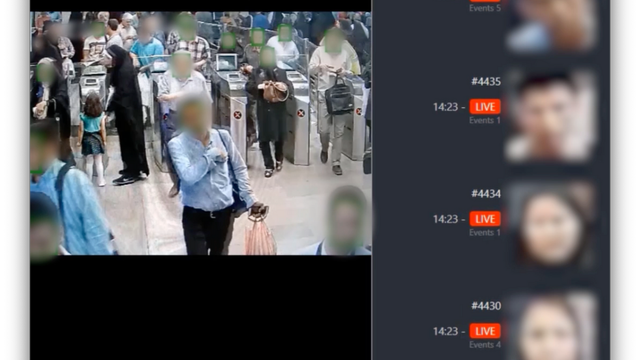
US-Präsident Trump fordert die Iraner auf, das Regime zu stürzen. Doch die Führung in Teheran hat einen gigantischen Überwachungsapparat erschaffen. SPIEGEL-Recherchen gewähren Einblick in das Spähsystem der Mullahs.