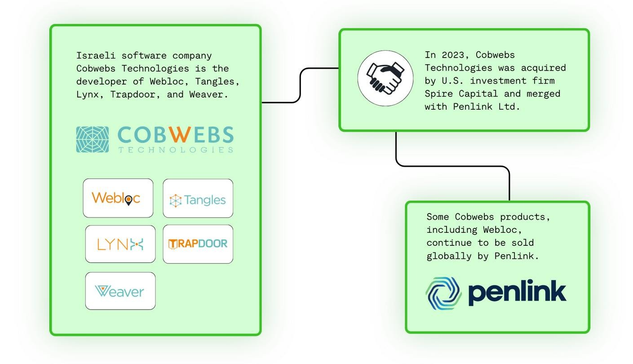
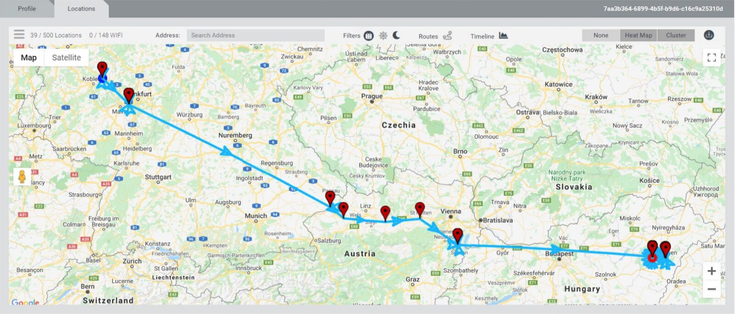
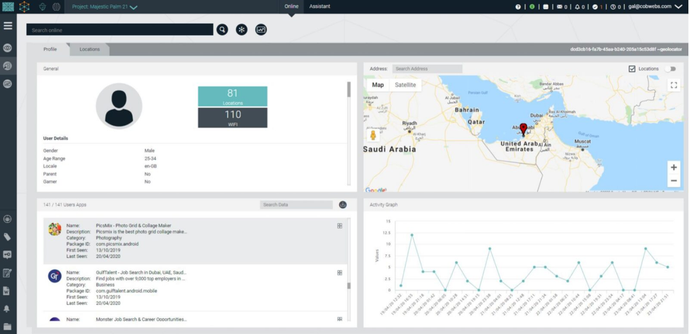
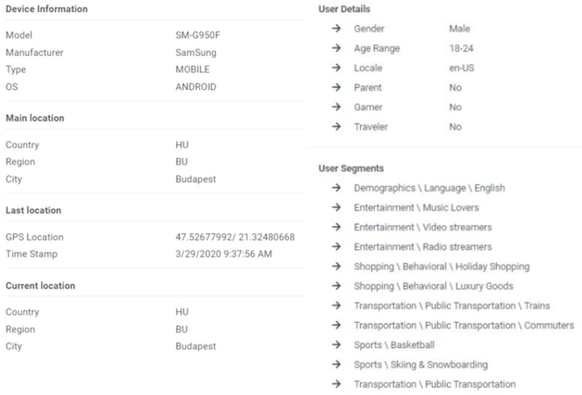
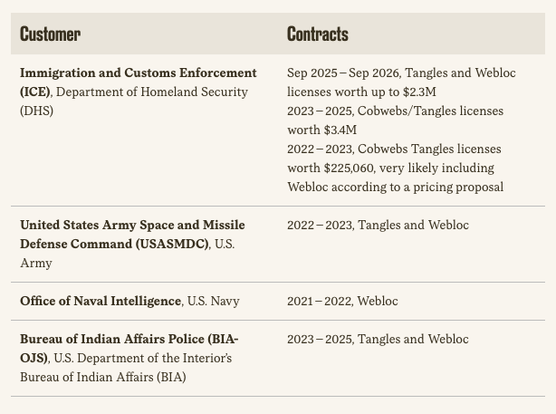
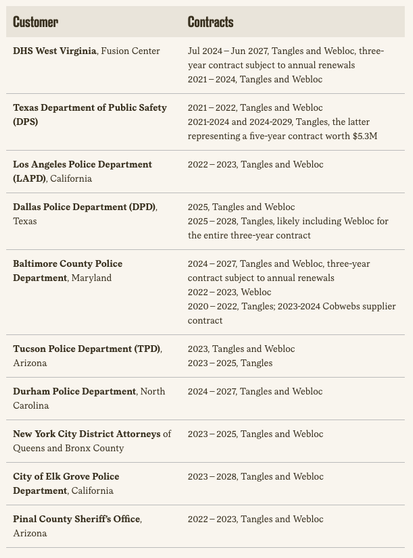
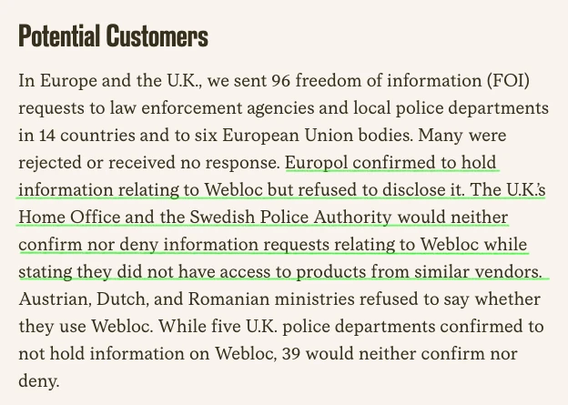
We publish a major Citizen Lab report on Webloc, an ad-based mass surveillance system that monitors the movements and personal characteristics of hundreds of millions people globally based on data obtained from mobile apps and digital advertising.
Customers include ICE, El Salvador and Hungary.
Our research shows that ad-based surveillance is now used by military, intelligence and law enforcement agencies down to local police in several countries.
Full report here:
https://citizenlab.ca/research/analysis-of-penlinks-ad-based-geolocation-surveillance-tech/