| Signal | @darkuncle.42 |
| The Rules | https://gist.github.com/darkuncle/d366a6c4323db64a7b761704d6f1ab95 |
| The Reading List | https://gist.github.com/darkuncle/42bdeed4503c6ccd9bdb025f6eb45fc6 |
| Profile photos | Zuma Beach and Henry Cowell Redwoods |
Scott Francis
- 1.6K Followers
- 1.6K Following
- 9.9K Posts
FEMA workers who sounded alarm over nation's disaster preparedness reinstated after 8 months
https://apnews.com/article/fema-whistleblowers-markwayne-mullin-disasters-214377203e959d4ddb5c811bd4cffd61?utm_source=flipboard&utm_medium=activitypub
Posted into Politics @politics-AssociatedPress

FEMA workers who signed dissent letter reinstated after 8 months
Fourteen FEMA employees who signed a public letter criticizing the nation's disaster preparedness have been reinstated after eight months on paid leave. The letter, known as the “Katrina Declaration,” criticized policy decisions by President Donald Trump's administration. Homeland Security Secretary Markwayne Mullin has reversed several policies of his predecessor, Kristi Noem, including a spending approval policy. The employees were initially reinstated in December but were placed on leave again. One of the reinstated workers expressed relief but remains concerned about the Federal Emergency Management Agency's future. It continues to operate without a permanent administrator.
RE: https://sauropods.win/@futurebird/116504568909057303
I didn't know about trap-neuter- return! (TNR)
https://en.wikipedia.org/wiki/Trap%E2%80%93neuter%E2%80%93return?wprov=sfla1
| Yes | |
| No / What on earth are you talking about Neil? |
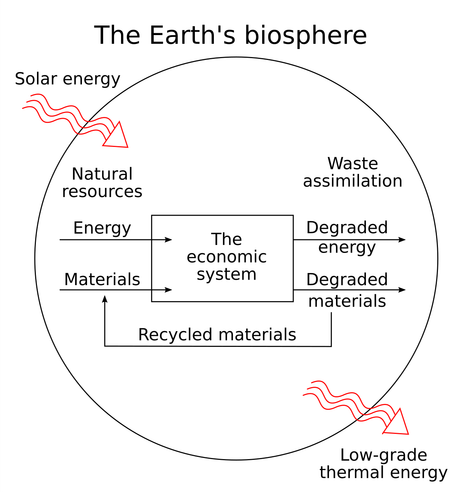
ECOLOGICAL ECONOMICS
Ecological economics is a diverse and controversial field. Any attempt to summarize it here would be woefully inadequate. But its central claim is that the human economy is a subsystem of the biosphere, and any economics that ignores this is doomed to fail in the long run [DF].
Indeed, the biosphere has been solar-powered and close to waste-free for billions of years. Our current human civilization has been running a fossil-fueled, waste-producing economy for about 200 years.
Ecosystems maintain stability through redundancy and diversity: multiple species perform overlapping functional roles, so that if one is knocked out others can compensate. Conventional economics prizes a specific kind of efficiency that tends to produce monocultures and brittle supply chains.
Ecological economics says the question isn’t *whether* we will transition from our current model toward something more like the biosphere, but whether we will do it by design or by collapse.
(1/n)
[DF] Daly, H.E. & Farley, J. (2011). Ecological Economics: Principles and Applications. Washington, DC: Island Press.
Special ACARS Drama Announcement:
We just wanted to take a moment, in light of recent news regarding Spirit Airlines, to pass on our best wishes to all 17,000 employees of the airline who are facing uncertainty this morning. That's a horrible thing for anyone to deal with and we hope you all find new opportunities soon.
Spirit provided plenty of ACARS Drama over the last couple of years, so, as a tribute, we decided to dive into the Archives and pick out our top 10 favorite Sprit Airlines ACARS Messages.
https://en.wikipedia.org/wiki/Confirmation_bias (Seriously what's happened is akin to the plot of Peter Hyams' "Capricorn One". The point is, Dawkins has no cognitive background, so he believes that the word guessing program called Claude is conscious and is his "friend". Parasocial relationship with chatbot)
Scott Aaronson (congrats on induction to Nat’l Academy of Sciences!) being extremely clear in his latest post:
“And I’d say that that makes my own moral duty right now ironically simple and clear: namely, to use my unique soapbox, as the writer of The Internet’s Most Trusted Quantum Computing Blog Since 2005(tm), to sound the alarm.
So, here it is: *if quantum computers start breaking cryptography a few years from now, don’t you dare come to this blog and tell me that I failed to warn you. This post is your warning.* Please start switching to quantum-resistant encryption, and urge your company or organization or blockchain or standards body to do the same.”