@ckfinite
- 34 Followers
- 93 Following
- 88 Posts
Welp, I'm going to be unemployed in about 2 weeks...unless I can find some work. :(
Here is my thesis on Security:
The diligent and reliable existence of locks, matters a lot more than their strength.
In trying to find how often lockpicking is a factor in burglaries, a huge number/majority of thefts were from behind no locks at all. Lockpicking is almost nonexistent.
Thieves simply try doors for being left open. Or just break a window.
This matched with my experience in Enterprise Security.
Penetrators got in through poking for trivial misconfiguration and lack of protection, not novel trespass.
They had millions of targets with a small % of success and won.
So I ask, why aren't we focusing on high assurance?
Because assurance is hard. It is not fun. It is not flashy. It fails silently. It supposes diligent attention.
Remediation is by definition beyond self-correction. The percentage of failures meets 85% SLA, even though it fails every month for three years.
Catastrophe is demure.
The modern Enterprise endpoint is almost always a massive distribution of responsibility. And in that denial of culpability, nobody is responsible for success.
The completeness of maintenance. The completeness of security configuration. The completeness of the agents that assure it.
It is the perfect failure.
Nobody owns actual success, just blame.
"ffmpeg" is a program that can do anything at all, but not on *your* computer, because the copy of ffmpeg on *your* computer just happens to be missing the optional-compile-flag library that does the thing you happen to want to do right this second.
Does anyone have any suggestions for cameras I can mount to either myself or a bicycle?
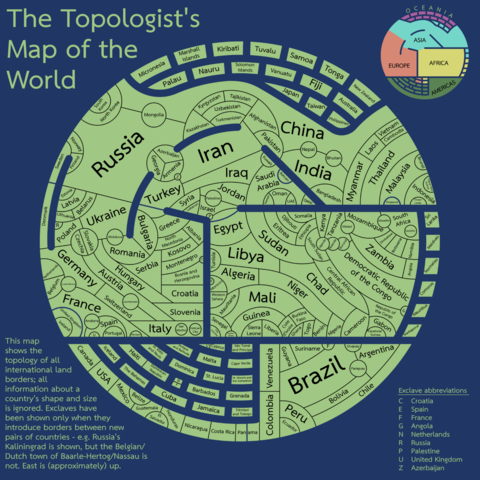
Really charming "topologists world map."
Forget size or position, this map *only* shows which countries border which other countries: http://tafc.space/qna/the-topologists-world-map/
FGM-148 Javelin
If you are considering running your own Mastodon server (or similar service) and it will be hosted in the United States, please read this general best practice guideline from the Electronic Frontier Foundation: https://www.eff.org/deeplinks/2022/12/user-generated-content-and-fediverse-legal-primer
#eff #electronicfrontierfoundation #law #legaladvice #bestpractices #fediverse #dmca #digitalmillenniumcopyrightact #section230 #corynnemchserry #rights #anonymity #copyrightlaw
User Generated Content and the Fediverse: A Legal Primer
A growing number of people are experimenting with federated alternatives to social media like Mastodon, either by joining an “instance” hosted by someone else or creating their own instance by running the free, open-source software on a server they control. (See more about this movement and joining...
pretty sure everyone here has already figured this out but here's part one, hey, I'm making one of them voron things.
https://youtu.be/tKOO65YNgYs
https://youtu.be/tKOO65YNgYs
I'm Building A Voron (and so should you!)
1/ New paper, recently published by the Communications of the ACM! “Subfield Prestige and Gender Inequality among U.S. Computing Faculty” with @hneutr @alliecmorgan @sz @DanLarremore and @aaronclauset:
We wondered: how do subfields and prestige shape demographic representation among computing faculty?
#diversity #computing #prestige #subfields #gender #inequality #faculty
A cryptobro DMed me to ask if I wanted to join his mailing list.
I spent slightly too long making this to send in reply.
I spent slightly too long making this to send in reply.