| https://twitter.com/charlesdardaman | |
| Github | https://github.com/CharlesDardaman |
| https://twittodon.com/share.php?t=charlesdardaman&[email protected] | |
| BlueSky | @charles.dardaman.com |
Chase 
- 1.2K Followers
- 317 Following
- 13 Posts
Imagine buying a #tesla after knowing their engineers are making fun of you
Tesla workers shared sensitive images recorded by customer cars
Tesla Inc assures its millions of electric car owners that their privacy “is and will always be enormously important to us.” The cameras it builds <a href="https://www.reuters.com/legal/elon-musks-2018-tweet-tesla-union-campaign-illegal-us-court-rules-2023-03-31/" target="_blank">into vehicles</a> to assist driving, it notes on its website, are “designed from the ground up to protect your privacy.”
Now that I’m caught up it’s absolutely wild that people want to block infosec.exchange because of feds making accounts while their #mastodon server lets you read the home timeline without logging in. I know you don’t like feds but your threat model is off
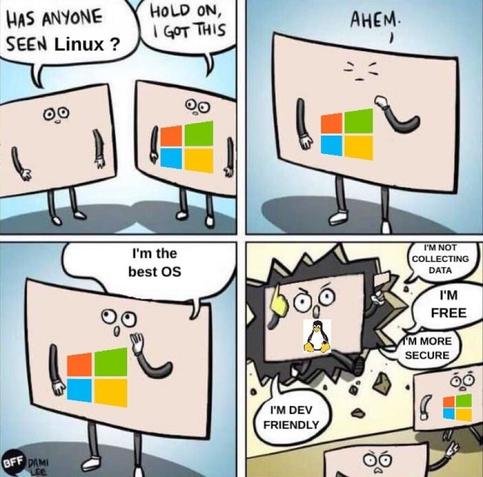
What cybersecurity awareness training boils down to.
If you want to learn how to be a #hacker then you need to focus on the process and methods that other hackers use rather than the toolset. A common thing I see people wanting to get into the field do is they obsess over the #tools used or the right version of #linux to use or whatever, but none of that matters at the end of the day if you don't have the repeatable process and methods down to correctly identify issues and exploit them in anything you run into regardless of your knowledge of the system going into it.
@tinker recently threw up an example of this for #web hacking https://infosec.exchange/@tinker/109349119268443920
Tinker ☀️ (@[email protected])
If you want to know how to hack into websites, I recommend reading attack narratives / methodology walkthroughs from folks like @gaz & @albinowax . Gareth ( @gaz ) goes into detail on his approach and coordination with James ( @albinowax ), his initial prodding, his attempts, his initial failures, his pivots, his initial possible successes and then, finally, his sussing out how to get his exploits to work. It's a wonderful guide in how to approach and become a website hacker with a current usecase as the example. Read the narrative and follow @gaz and @albinowax . https://portswigger.net/research/stealing-passwords-from-infosec-mastodon-without-bypassing-csp #hacking #TeachMeToHack #WebAppPentesting #infosec