Software Engineer
I believe in "The Hacker Ethic"
Feel free to request to follow. I approve based on gut feeling
| Hackspace | @muccc |
| Languages | German, English |
| DECT | 3423 |
Software Engineer
I believe in "The Hacker Ethic"
Feel free to request to follow. I approve based on gut feeling
| Hackspace | @muccc |
| Languages | German, English |
| DECT | 3423 |
+ 100% remote wenn Du das möchtest
+ "Alles außer Windows"
+ kein Teams, Zoom oder WebEx
Mehr als diese drei Zeilen bräuchte es in keiner IT-Stellenausschreibung, um wirklich gute Leute zu bekommen.
Bundesinnenministerium stoppt Fördergelder für Anti-Extremismusprojekt
Die Gründerin eines Anti-Extremismusprojekts kritisiert Aussagen des Kanzlers, darauf stoppt das Innenministerium die Finanzierung - trotz Protestes der Bundeszentrale für politische Bildung. Das belegen Dokumente, die Report Mainz vorliegen.

Die Gründerin eines Anti-Extremismusprojekts kritisiert Aussagen des Kanzlers, darauf stoppt das Innenministerium die Finanzierung - trotz Protestes der Bundeszentrale für politische Bildung. Das belegen Dokumente, die <em>Report Mainz</em> vorliegen.
RE: https://23.social/@leyrer/116278329580225573
Business-Idee: bei börsennotierten Unternehmen als unabhängiger #Consultant Cloudmigration und #KI pitchen.
Wenn's jetzt noch auf fruchtbaren Boden fällt, deren Aktien mittel- oder langfristig shorten und zum nächsten Unternehmen weiterziehen.
Pension gesichert. 👍💰
#Trivy got compromised on thursday and released a backdoored new version, which was rolled back. We spent the entire friday in incident response mode. Now they got compromised again over the weekend.
I have a lot of sympathy for people under pressure during an incident, but for fucks sake, having a security tool get compromised three times within two months is just completely bonkers. We spent more time remediating security issues caused by our security tooling than any other cause. And the fact that there wasn't any official communication on friday means that we had to rely on third-party writeups, which were missing critical information like exact docker container digests and time ranges of the compromise. This made incident response completely miserable.
Anyway. Trivy 0.69.4, 0.69.5, 0.69.6 were all compromised with infostealer malware. Do what you have to do. There are several decent writeups:
- https://www.stepsecurity.io/blog/trivy-compromised-a-second-time---malicious-v0-69-4-release
- https://www.wiz.io/blog/trivy-compromised-teampcp-supply-chain-attack
- https://labs.boostsecurity.io/articles/20-days-later-trivy-compromise-act-ii/
And Trivy has an advisory on their GitHub that covers last thursday, but not the second compromise over the weekend: https://github.com/aquasecurity/trivy/security/advisories/GHSA-69fq-xp46-6x23
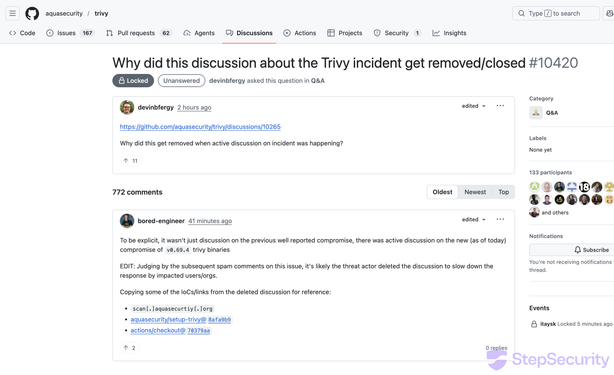
On March 19, 2026, trivy — a widely used open source vulnerability scanner maintained by Aqua Security — experienced a second security incident. Three weeks after the hackerbot-claw incident on February 28 that resulted in a repository takeover, a new compromised release (v0.69.4) was published to the trivy repository. The original incident disclosure discussion (#10265) was also deleted during this period, and version tags on the aquasecurity/setup-trivy GitHub Action were removed. Trivy maintainers deleted the v0.69.4 tag and Homebrew downgraded to v0.69.3. The following is a factual account of what we observed through public GitHub data.
OH: Are the mate crates structural? Oh wait yes they are!