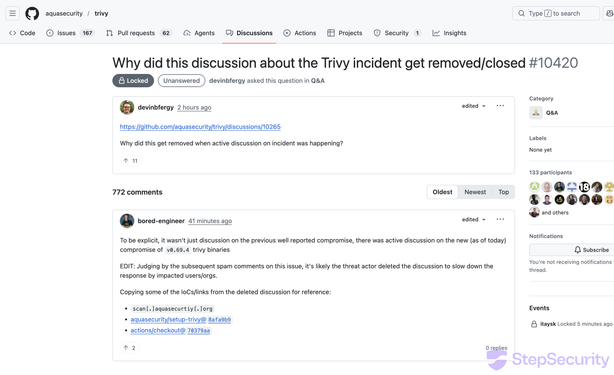
#Trivy, a popular open-source vulnerability scanner, was compromised - attackers hijacked 75 version tags in #GitHub Actions to deliver an infostealer.
It ran in CI pipelines, stealing creds and tokens, exfiltrating data:
#SoftwareSupplyChainSecurity
👇
https://thehackernews.com/2026/03/trivy-security-scanner-github-actions.html
 🐘
🐘