#ESETresearch's Eric Howard will be presenting at Botconf. Join him in Reims, France to hear about “GopherWhisper, Uncovering an APT’s secrets through its own words” on Apr 15 at 17.15 CEST. For more information, check out https://www.botconf.eu/botconf-2026/#id_schedule
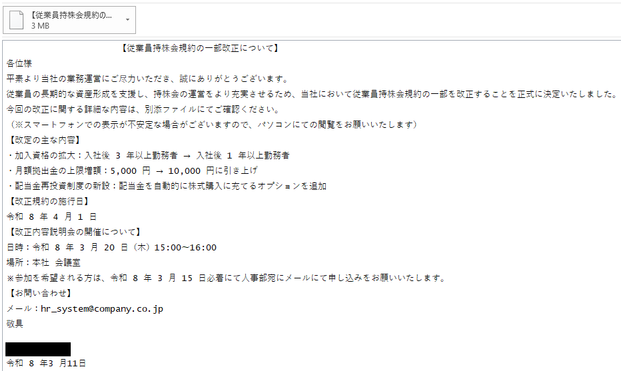
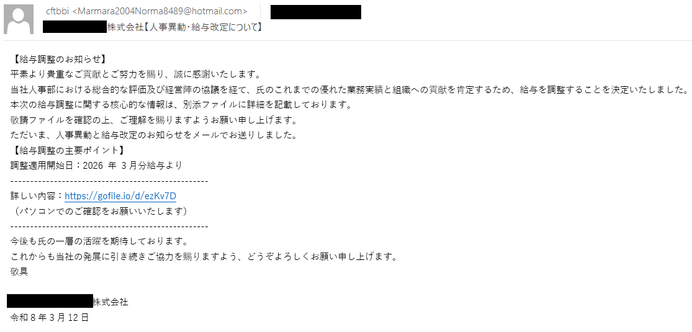
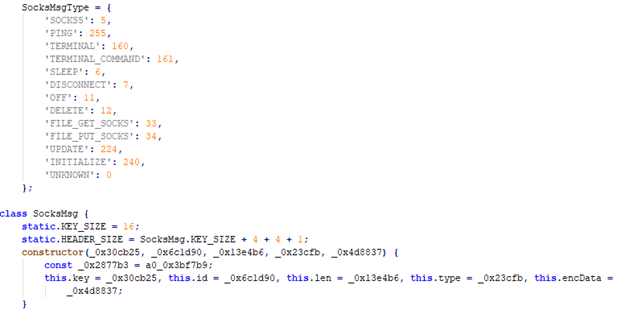
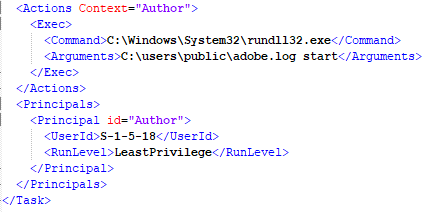
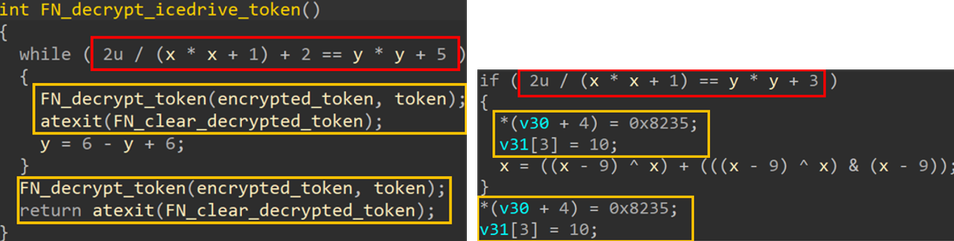
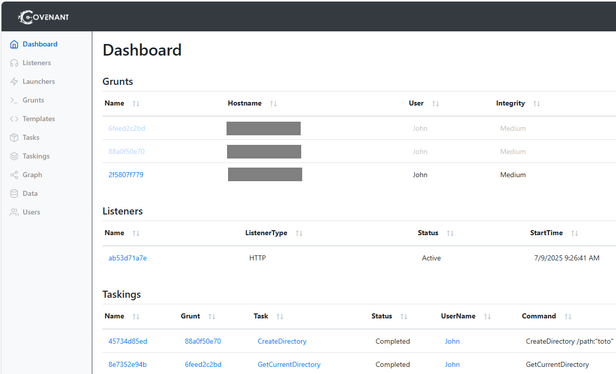
New China‑aligned APT GopherWhisper: first seen in 2025 deploying backdoor LaxGopher inside a Mongolian government institution. The group’s backdoors abuse legit services for C2 (Slack, Discord, Microsoft Graph). Hardcoded tokens let us peek into ops and post‑compromise activity.
We recovered 5K+ C2 messages (activity since 2023‑11), mapped tools (LaxGopher, RatGopher, BoxOfFriends, JabGopher, FriendDelivery, CompactGopher, SSLORDoor), and saw exfil via file.io, presentation will provide defender tips. Full research will be later released on WeLiveSecurity.com
New China‑aligned APT GopherWhisper: first seen in 2025 deploying backdoor LaxGopher inside a Mongolian government institution. The group’s backdoors abuse legit services for C2 (Slack, Discord, Microsoft Graph). Hardcoded tokens let us peek into ops and post‑compromise activity.
We recovered 5K+ C2 messages (activity since 2023‑11), mapped tools (LaxGopher, RatGopher, BoxOfFriends, JabGopher, FriendDelivery, CompactGopher, SSLORDoor), and saw exfil via file.io, presentation will provide defender tips. Full research will be later released on WeLiveSecurity.com